Multi-Factor Authentication Should Be HARD
How difficult is it for a computer (or a complete stranger) to validate the true identity of a person they don’t know? Very difficult, it turns out, especially when others may be trying to imitate them. To solve this challenge, identity and access management (IAM) programs increasingly rely upon a combination of multi-factor authentication (MFA) and risk-based authentication (RBA). Taken together, these programs look at a combination of four categories of data, the first letters of which form the acronym HARD.
H stands for something you HAVE. This category is no different than requiring keys to your front door, which in the digital world often takes the form of having chip-enabled (or virtual) smart cards or USB dongles.
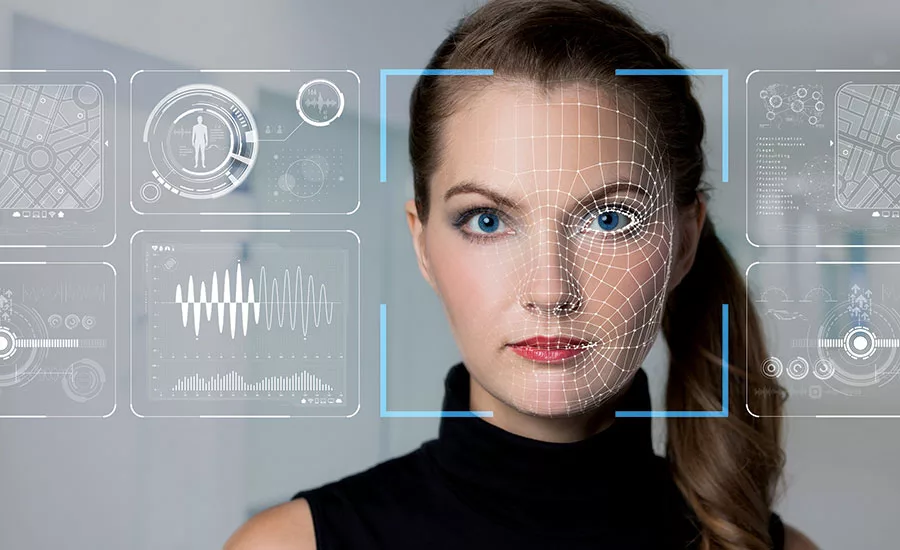
A is something you ARE. These are inherited traits. Today’s consumer products commonly use fingerprint and facial recognition biometrics.
R is something you REMEMBER. Although passwords are commonly used as the first factor, they have proven to be the most burdensome and the easiest to compromise.
D is something you DO. These are contextual identifiers, and can include geo-location data, web-browsing and purchasing habits, and even quasi-biometric characteristics like typing patterns on a computer keyboard. This category typically is considered a part of risk-based authentication and, owing to gains in big data analytics, holds the greatest promise for removing the burden of authentication from the user to the verifier.
The key to implementing a reasonable IAM program is to take advantage of as many of these factors as possible, while balancing the potential harm of mistaken authorization against the financial costs and diminished user experience of cumbersome approaches. Increasingly though, deploying at least two types of the first three listed factors (what you have, are or remember) is becoming not only a best practice but a legal requirement. PCI-DSS now demands MFA for certain types of administrative access, the Department of Defense recently increased MFA standards for contractors, and state and federal regulators are viewing MFA as a foundational element of “reasonable” cybersecurity.
Still, picking the right solution is not obvious. There are dozens of methodologies, and hackers can and routinely do compromise many of them. Understanding key selection criteria, therefore, is important. First, authentication factors should be independent of one another so that access to one does not provide access to the other. Second, the channel used to obtain and/or submit secondary authentication factors ideally should be different (“out of band”) from the primary one in the event the first is compromised. In high-risk environments, consider NIST’s view that SMS, VoIP, and email are not secure enough to serve as secondary authentication channels. Third, users should be given or denied site access only after the entire authentication process is complete. This prevents hackers from determining which factors failed or succeeded. Finally, stay current. As MFA technologies and methods mature, your program will improve as well.
To learn more, check out the NIST Special Publication 800-63 series, the PCI Security Standards Council Multi-Factor Authentication Guidelines and MITRE’s Multi-Factor Authentication for eCommerce.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







