On Track with ID Tech


All three hit on solutions that bundle emerging identification technologies with a variety of existing and leading edge communications mediums.
Pullo, president of Metro Fuel Oil Corp., works with Satellite Security Systems (S3) of San Diego and that firm’s FleetGuard application to secure and monitor 16 service vehicles and 40 fuel and oil tankers. FleetGuard desktop software works with S3’s GlobalGuard to view, command and control fleet vehicles. The security communications system uses cellular ReFLEX technology and GPS to provide up-to-the-minute vehicle location and control of fixed and mobile assets. Well aware of the homeland security concern that a fully loaded tanker truck could be used as a terrorist weapon, the system continuously provides security analysis.
“In our business it’s imperative to protect employees, customers, the public and the company itself,” Pullo says. “If the unthinkable ever happens and one of our vehicles is hijacked by terrorists, it is very comforting to know that the security system will respond on our behalf and work with law enforcement to take control of the vehicle and shut it down before any damage can be done.”

Integrating Technologies
Metro Fuel Oil Corp has been at the forefront of combining identification and communications technologies, having installed GPS prior to the Sept. 11 terrorist attacks and supplied emergency services immediately after the attacks. Metro recently upgraded from an old GPS system to FleetGuard based on additional features and the system’s remote engine shutdown capability, according to Pullo. Its fleet of 40 tanker trucks will be outfitted with the system so that in the event of a hijacking or other security breach, the truck can be stopped and controlled. In addition, Metro’s service vehicles will have tracking capabilities in order to increase business efficiency and route planning.“S3 is now working with leading trucking companies on both coasts,” said S3 COO John Phillips, who also noted that “the need to protect and secure these fleets is a paramount concern to these company executives.”
Bus companies, local school districts and other organizations also can benefit from identification, tracking and control systems. Such users can communicate with, monitor, track, analyze and control the movement of virtually any object in transit. Integration of two-way satellite communications, an on-board computer and GPS allows users to send data back and forth from a central command unit or monitoring center while being continually alerted to new or dynamic changes.
In Bogotá, Identec Solutions of Kelowna, British Columbia, worked with WM Wireless & Mobile Ltda., a local company, to deliver a radio frequency identification (RFID) system to track the 23,000 privately owned transit buses that operated in the city.
The city’s transit bus infrastructure was creating high congestion along major routes where buses were competing for riders, leaving other areas of the city without service with those buses operating with low ridership. To control transit activity, offer better public access and improve transportation security, the local government determined it would allocate a specific region to each bus and use an RFID system to track and verify bus movement. In 2003, Bogotá’s secretary of transit and transportation issued a regulation stating that each transit bus must be equipped with an RFID tag in order to operate. The key factor was the system’s ability to consistently and accurately read tags at a distance of at least three meters with a handheld device.
“This project is a great example of where our RFID system is designed to be used and helps build the case that RFID is a reliable identification method to address real-life problems” said John Kingsmill, president of Identec.
WM began installation last November, tagging buses on the passenger-side dashboard with an active tag. Transit officers were issued rugged handhelds to read the tags. Similar to speed traps, officers set up random inspection points and pull buses over to verify the tag ID and city region match.
Not only has the system gained acceptance among the community and transport companies, it has led to substantial social and economical benefits by reducing daily commute times from four hours to one hour.
ID and communicate
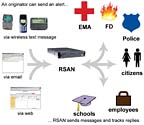
Virginia’s King George County is trying a system that combines identification and communications to alert necessary individuals during an emergency. When activated, the King George Alert System (KGAlert) homes in on important personnel, delivering a warning message to mobile communication devices and computer e-mail. Powered by the Roam Secure Alert Network (RSAN), KGAlert functions as an emergency communication and terrorism early warning system that should enable first-responders, government agencies, private industry officials and the public to communicate reliably under difficult circumstances.Emergency management officials will be able to use KGAlert to reach thousands of county employees and citizens spread across this rural Virginia area via their mobile telephones, pagers and Blackberries, as well as through e-mail. Officials will communicate important emergency information, such as severe weather warnings and watches, changes to the federal terror threat level and other important information during a crisis, power outage or major emergency. The county purchased the system from Arlington, Va.-based Roam Secure using federal homeland security grant funds.
“We saw how other jurisdictions were using such systems during recent emergencies and realized it would be a valuable tool for King George County,” said Emergency Management Coordinator, Wendy Shepherd. “Rural counties like King George need to be prepared for all-hazards incidents and KGAlert will help improve our communication capabilities.” The HHS has a similar alert network for emergency communication among its senior officials and hundreds of employees. The HHS will operate its system out of the Secretary’s multi-million dollar, state-of-the-art command center, which made its debut in December 2002. The command center combines various forms of communication, including redundant ground-based and satellite systems, computers, radios, plasma televisions and other high technology equipment, and allows officials to safely coordinate bio-emergencies occurring anywhere in the United States. HHS officials will use the emergency alerting capabilities to reach its top personnel on their mobile devices. Executives will receive news regarding bio-terror attacks, developing health emergencies and changes to the federal terror threat level.
Public health emergencies require immediate action, so it is essential to HHS that they will be able to contact hundreds of officials via multiple devices in seconds. “The system’s redundant delivery channels and reply-tracking features make me confident our personnel will receive critical alerts and allow us to follow up if we detect no response,” said Dean Ross, director of the Secretary’s command center.
Sidebar: Identification is a first step to better response.
ID Tracking of the BadState and local officials responsible for prisons, jails and probation programs are taking a renewed look at identification and GPS.
As these agencies face fewer budget dollars, more offenders qualify for probation and communities are demanding better accountability. Systems that combine identification and tracking technologies, although expensive, are catching on.
One example: The state of Florida now is debating a $35 million contract to equip people on probation with an electronic bracelet that identifies the wearer and tracks the person through global positioning. In a system called VeriTracks from Veridian Corp., of Arlington, Va., the bracelet really is a box that collects data as the person moves around. Placed in a docking station nightly, the box uploads information to a central monitoring station. Veridian is a General Dynamics company.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




