Go Beyond What’s Enough
Proper card design can help reduce this vulnerability. Incorporating security elements that are difficult to forge, yet easy to authenticate should be the first consideration in a secure card design.
The most basic element of a secure card is a color photograph.
Beyond photos, employee numbers, barcodes or other identifiers printed on the card, there is a huge range of visual elements that add security.
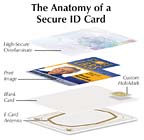
Holograms are most commonly seen in overlaminates, a clear film applied to a printed card’s surface. Overlaminates can contain an off-the-shelf holographic design, or a custom design for even greater security.
Alternatively, consider reverse image printing technology. In reverse image technology, the printer first prints images onto a special film that is then fused into the surface of a blank card through heat and pressure. Because the printhead in a reverse image printer prints only on to the flexible film and not the card surface itself, these cards do not suffer image quality problems due to surface irregularities.
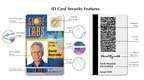
Once the visual security and functionality layers have been determined, designing the card graphics comes next.
To begin the graphic design process, some find it helpful to divide the card into a grid, placing the fixed elements (i.e., smart chips, visual security elements or logos), into position first. Determining whether the card orientation will be horizontal or vertical is important, as is determining the size and relationship of the identifying elements such as photo, ID number and signature. One factor companies often overlook is whether or not there will be a hole punched in the top of the card to accommodate the badge clip. If so, it is important to allow for it in your design.
Don’t be afraid to use color, but avoid very dark colors because they affect readability. Likewise, pastel backgrounds can look washed out. Bright, primary colors work best. Consider using a textured background rather than a solid color to minimize surface flaws.
For most ID cards, the photo is the primary feature. That’s why it is important to use high-resolution images (at least 300 dpi) and to make the photo as large as possible.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!


