Ivy-league Security
When a student at Harvard University had her picture identification card either lost or stolen, she quickly reported it to the proper authorities. But within days, the card, by then deactivated, was being used in a vain attempt to open doors across campus.
Each attempt to enter a restricted area was noted immediately through the access control system monitored by the Harvard University Police (HUP). HUP officers monitored the events and moved quickly on yet another failed entry attempt. The person responsible was apprehended and the card confiscated.
All students, faculty, staff and alumni are expected to carry university-issued photo identification badges. In addition to allowing access to appropriate buildings, the cards also are used for library, food services, recreational and various other purposes.
Founded in 1636 in Cambridge, Mass., Harvard is the nation’s oldest institute of higher learning. Yet it has provided its campus police with some of the most recent, technologically advanced tools, such as smart cards, access control, dome cameras, digital video recorders and plasma monitors to protect the more than 30,000 students, faculty and staff members.
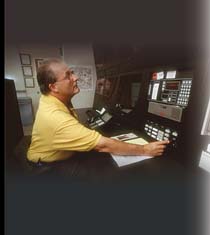
Charles Mongue, HUP’s security systems coordinator, points out there were two major goals for the access control system installed in the winter of 2002. First is to provide access control through the university police headquarters. The second goal is to provide police dispatchers with one system to respond to all alarms throughout the university.
Venerable Security
Last winter, HUP moved to a new building on the main Cambridge campus and upgraded its security system based on the C•CURE 800 access control system from Lexington, Mass.-based Software House, a part of Tyco International’s Fire & Security Division. C•CURE 800 provides integration with critical business applications including: CCTV and digital video, visitor management, time and attendance and third party devices such as fire alarms, intercoms, burglar and other alarms. The system monitors more than 5,000 alarm points, including about 1,500 card readers, 14 surveillance cameras and about 150 emergency calls boxes.The HUP installed two D6600 receivers from Salinas, Calif.-based Radionics/ Bosch Security Systems to filter all alarms into the C•CURE system. The second receiver is redundant and becomes operable with a switch of a key should the first receiver fail. Two C•CURE client stations provide dispatch officers with all relevant data related to alarm events. These stations are manned around the clock. Printers are connected to the D6600s to provide a hard copy of all alarms as a backup.
According to Mongue, officers are dispatched to investigate all alarms.
“We’re here to serve the students and staff and it’s not our job to be making decisions about which alarms deserve a response and which don’t,” he says.
Harvard University is a highly decentralized institution. In addition to the main Cambridge facilities, there are three other campuses located within the general area. The other three campuses, two of which are located in nearby towns, have their own separate security systems and guard staffs. There are 21 different access systems just on the Cambridge campus. Eight of those systems are now linked to the HUP. Those eight represent some of the larger departments and the majority of the dormitories.
“We tried to make it easy and economical for the departments to get their monitoring through the university police,” says Rich Reidy, project manager for Avon, Mass.-based Mac Systems, the systems integrator for the recent upgrade.
Doing Their Homework
Mongue says the HUP maintains daily contact with all facility managers not a part of the department’s security system. However, he observes the long-term goal is to centralize all security systems and related activities through the university police. The process may take years to fully complete.The HUP is also responsible for security for its own facilities, located in a six-story building on the Cambridge campus. The police operation occupies the top floor and the basement parking area. Other university administrative staff use the remainder of the building.
The building is accessible to employees and the public from 8 a.m. to 6 p.m. Monday through Friday. Employee access doors are automatically locked and unlocked by the C•CURE system. Other doors remain locked at all times. To gain entry after hours, or on weekends and holidays, employees or students must use one of the 150 call boxes from Chicago-based Talk-A-Phone Co. to contact a police officer. All calls are recorded. The call boxes are automatically polled five times a day to ensure that they are working properly. Also one of 10 fixed cameras located around the building provides video of the person wishing to enter. The cameras are from Sony Security Products of Park Ridge, N.J. Two dome cameras from San Diego-based American Dynamics, part of Tyco’s Fire & Security Division, monitor the basement garage.
Once inside the building, a keypad allows employees to stop at their selected floor. If no code is entered, the elevator is programmed to stop only on the sixth floor – police headquarters. Later this year, the keypad is expected to be replaced with a card reader.
The fixed cameras are on a time schedule for continuous recording during business hours. At all other times, they record only when motion detectors note movement. The dome cameras are on constant automatic tours of the garage, with a normal record rate of 2.5 images per second. When motion is detected, the record rate jumps to 30 images per second. The cameras have been placed to allow for full video coverage of suspects from the time they enter the basement until they have completed the booking process.
Video Meat and Potatoes
All video is routed through an American Dynamics MegaPower 48 matrix switcher and recorded by an American Dynamics Intellex digital video management system. The MegaPower 48 Matrix switcher/controller system incorporates high-end features into a cost-effective switcher/controller that’s optimized for small to mid-sized applications. The Intellex is an intelligent digital video management system that combines multiplexing, alarm/event detection, video, audio, text and recording. The system simultaneously displays live or playback video, with or without audio and text, hosts multiple remote users, archives, and performs comprehensive video searching all while recording multiple video, audio and text streams.HUP officers view the video on one 42-inch and/or four 20-inch monitors from Sony.
Network client software, also from American Dynamics, allows officers in the HUP headquarters to remotely view video associated with live alarm events or pre-recorded video from 10 other Intellex units located across the university. Mongue says this allows the HUP to provide current information to officers dispatched to an alarm, as well as to gather recorded video for investigative purposes.
Also located within HUP headquarters is a contraband room, where evidence collected during arrests and investigations is stored. This room has a triple layer of protection. There is a Software House RM1-MP card reader at the door, as well as a hand geometry reader from Hollywood, Fla.-based RSI. Burglar alarms and motion detectors are inside. Only two people – the chief of police and a ranking detective – have access to the room.
Mongue believes the department’s new location and security system has worked very well.
“Now we have room to expand and the C•CURE system lets us know immediately where an alarm event is taking place. We are very pleased with the way things have worked out for us," says Mongue.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





