What Your CEO Thinks: As Recession Recedes, Security Execs Feel C-Suite Spotlight

How does John Imhoff, director, Office of Firm Security for Ernst & Young, sell his security ideas to the C suite? “By communicating security’s value…and establishing a routine that creates the expectation of essential information on a regular basis.”

It’s important to always manage the relationship with the C-suite, contends corporate leadership consultant Jean Kelley.
A complementary Conference Board report provides a reason: in a challenging economy, the C-suite is often more protective of staff, though insistent on squeezing budgets. With a glimmer of silver emerging from the clouds, these same executives can spend more time on performance evaluation.
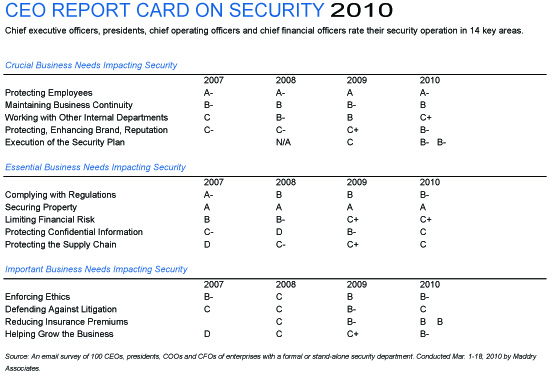
Since 2007, Security magazine – through security industry research firm Maddry Associates – annually surveys 100 enterprise CEOs, presidents, chief operating officers and chief financial officers asking them to score their security operation in 14 categories. Again this year, they were also asked to label the importance of those 14 elements from critical and essential to important.
Critical elements include protecting employees and help with maintaining business continuity – both life or death assignments for people and the enterprise. Essentials include regulation compliance and securing property. The former has gotten more challenging, thanks to the growing number of federal and state homeland security requirements emerging by type of business or based on critical infrastructure. Important elements include ethics and defending against liability, often assignments shared by others in the enterprise.

Always sell yourself, your ideas, your value, and your ability to the CEO, advises business management author Patricia Fripp.
Report Card Comparisons
The 2010 CEO Report Card and its comparison to 2007-2009 ratings appear elsewhere in this article. While the Report Card breaks down CEO expectations into 14 elements, C-suite executives look at the big picture as well as the critical details.Chuck Robey, with 40 plus years of professional diversified service including management positions, believes that, for some C-suite executives, there still needs to be a mindset change. In these cases, “top corporate management may see security as holding to an outdated philosophy of ‘controlling and enforcement’ rather than a philosophy of ‘service and consultation.’ When this outdated corporate fish bowl syndrome occurs, security generally has two basic options, either positive or negative. Obviously, in order to survive in this contemporary security society, the response must be positive” and proactive, Robey contends. Check out his Proactive Road article at www.securitymagazine.com.
John Imhoff, director, Office of Firm Security, Ernst & Young LLP, takes an all-encompassing view shared by most CEOs. “C-suite executives should view security as an integral part of operations providing seamless protection for people, assets and continuity in everything the company does. By seamless I mean built in, not layered on.
“Take for instance security awareness training for newly hired staff. Clear, unequivocal messaging concerning personal responsibility for protecting assets and emergency plan awareness must be a part of every orientation. New hires must then see that the message is taken seriously in the work environment. Delivering this information six months later is too late to inculcate security habits,” he says.
And both the enterprise and the security operation constantly measure performance in one way or another.
“There is no single metric for measuring the effectiveness of a program as diverse as security. Inevitably, it requires a number of disparate measures. For C level reporting, these must be consequential indicators tied to the greatest areas of concern (vulnerability) and limited to a few elements easily analyzed over time and relevant to organizational objectives,” comments Imhoff.
Back to the Basics
It’s a matter of basics when security operations are evaluated by top management through their understanding of the relationship of risk, threat and vulnerability, then prioritizing security decisions, according to John Culwell, a security executive with the City of Phoenix water services department. “Security must not interfere with the business needs of an organization; if it does, it cannot be effective because executive management will revisit the risk, threat and vulnerability relationship. We all (security professionals) understand that risk is something you take, threat is something you face and vulnerability is something you accept; our bosses expect us to mitigate, prevent and reduce,” says Culwell.But “executive management’s understanding of that reality is a major challenge,” Culwell adds.
On the topic of challenges and change, however, while top executives are pressuring security on performance issues more deeply, there is no doubt that economic times are somewhat changing in 2010 compared to 2009 and 2008.
For instance, CEOs appear to be emerging from recession mode and priming for a return to growth, according to results of The Conference Board CEO Challenge 2010 Survey, which were reported in February. “Both the year-on-year movement and rank order of challenges suggest that CEOs’ focus has moved from crisis reaction to preparations for recovery,” says Jonathan Spector, CEO of The Conference Board. “Clearly, CEOs in the United States in particular are returning their focus to the road to growth.”
That also marks a shift for security.
Each year, The Conference Board CEO Challenge Survey asks hundreds of senior executives to identify and rate their most pressing concerns. But production of the 2008 report was stopped and the survey refielded in late 2008 in response to the exploding global financial crisis. Nearly 200 CEOs, chairmen, and company presidents updated their responses, offering a unique “pre” and “post” insight.
With no control over a turbulent global economy, CEOs had retrained their sights onto “bread and butter” survival issues, while longer-term challenges, especially in talent management, were de-emphasized.
CEO Worries Jump Back and Forth
“In that late 2008 survey, worries about global economic performance, business confidence, geofinancial instability, and integrity of capital markets leapt up into CEOs’ Top 10, and each has now dropped at least 10 places,” observes Linda Barrington, one of the report’s authors. “This year, all the challenges that jumped into the Top 10 in the crisis have now jumped back out.”The critical issues of excellence in execution and consistent execution of strategy by top management have consistently remained at the top of The Conference Board list.
In the Security magazine survey, C-suite executives were asked to rate “execution of the security plan” and the score mostly held its own compared with last year.
In The Conference Board study, moving up were corporate reputation for quality products/services, and stimulating innovation/creativity/enabling entrepreneurship.
On the Security magazine study side, C-suiters rated security’s protecting and enhancing of the brand and enterprise reputation a little higher this year compared with 2009.
John Dodds agrees with the importance of enhancing the brand and the shifts due to the economy.
“When the world emerges from the depths of the worst recession in two generations, it will certainly be a different and more difficult place to effectively manage a corporate brand,” says Dodds, director, global brand and communications, Air Products, and an expert on corporate brand management. “Companies simply won’t be able to do things the way they always have.”
So enterprise security leaders have a real role to play.
The global recession coupled with cases of unethical corporate behavior worldwide have eroded trust in business, and consequently, in corporate brands. In previous downturns, smart companies successfully positioned themselves and their brands to emerge stronger, healthier and more primed for growth than when the economic downturn began, says James Andrews of Boston Consulting. Although the C-suite and the board of directors instinctively know there is positive value in corporate name recognition and a strong brand, they are unsure how that relates to the bottom line.
Focus on the Bottom Line
Security must always see itself as a contributor to the bottom line. “Know what makes the business move and tick. Always ask yourself what is the business in business for,” suggests James Francis, vice president, security consulting services at T&M Protection Resources, who many times bridges the gap between the CSO and the C-suite.But such happenings as workplace violence incidents, infant abductions, college hazing and safety violations can harm the value of a brand as well as a corporation’s stock price, observes Barry Nixon, executive director for the National Institute for the Prevention of Workplace Violence, Inc. Nixon was a speaker at this year’s first iSecurity online conference and exhibition, held by Security magazine. His presentation and other events from iSecurity are available archived at www.sdmmag.com/isecurity
Both the Security magazine CEO Report Card this year and other studies show the growing importance and potential headaches due to government regulations, ranging from local and state mandates to national, international and industry-specific ones.
In The Conference Board study, the challenge of government regulation also made significant leaps in the United States, particularly in the financial services industry. “Complying with regulations,” an essential business need in the Security magazine survey, garnered a rating a bit lower than last year, but enterprise security executives interviewed for this article suggest that with increase regulatory pressure, security is just one of a number of departments and layers in corporations with responsibility and that chief financial officers, chief information officers and corporate attorneys often play a larger leadership role.
The more critical rating of security by C-suiters in the Security magazine study also reflects a noticeable shift to more concentration by top management on what’s called strategic workforce planning (SWP). So, as the recovery progresses, employers generally swing focus from cutting labor costs back to preserving talent and investing in key segments of their workforce – issues at the very heart of SWP and, by inference, security.
A Return to Building the Business
“Employers who’ve been forced to focus on reducing headcount will return to deciding whether to buy, build, or rent the skills necessary to meet future business needs,” says Mary Young, author of a report, Strategic Workforce Planning in Global Organizations.“The economy’s impact on SWP is likely to be moderated by the level of credibility, acceptance, and integration that SWP had attained before the economic crisis turned things upside down,” Young adds. “In companies that were just getting their feet wet with SWP, the global economic downturn may have put a halt to these efforts, although only temporarily. The same is true in companies where immediate financial pressures required that SWP shift from long-term planning to short-term problem-solving. But in companies where SWP was well established, SWP served as a critical tool for managing through the economic crisis.”
“Strategic workforce planning enables companies to make these decisions based on sound data and analytics,” she adds. Her report finds that, while some SWP strategies work fine on a global scale, others need regionalization to accommodate differences in demographics, skills levels and labor costs. One case study spotlighted by Young shows how, in just four years, 3M moved from knowing very little about its workforce to clearly understanding global characteristics and trends, and important regional differences.
What about Ethics?
With enforcing ethics one of the 14 Security magazine elements, a more overall issue is the need for senior management and boards to move proactively to better integrate integrity and corporate strategy. “The time for integrity to be integrated into strategy has come,” contends Andrea Bonime-Blanc, general counsel, chief compliance officer, and corporate secretary of Daylight Forensic & Advisory LLC, who co-authored a recent topic report with Jacqueline E. Brevard, vice president and chief ethics officer of Merck & Co. Bonime-Blanc and Brevard are members of The Conference Board Global Council on Business Conduct, which joins company representatives from around the world to address issues of ethics, compliance, governance and stakeholder engagement.An umbrella over all elements of the security mission and as understood by the CEO boils down to two words – risk management.
Risk management is an increasingly important business driver and stakeholders have become much more concerned about risk. Risk may be a driver of strategic decisions, it may be a cause of uncertainty in the organization or it may simply be embedded in the activities of the organization, according to the Association of Insurance and Risk Managers.
An enterprise-wide approach to risk management enables an organization to consider the potential impact of all types of risks on all processes, activities, stakeholders, products and services.
Implementing a comprehensive approach will result in an organization benefiting from what is often referred to as the “upside of risk.” For all types of organizations, and especially for security executives, there is a need to understand the risks being taken when seeking to achieve objectives and attain the desired level of reward and the overall level of risk embedded within processes and activities. It is also important to recognize and prioritize significant risks and identify the weakest critical controls.
Dressing up Risk Management
“The concept of enterprise security risk management, an integrated approach to identifying, evaluating and mitigating risk, once implemented, is both sustainable and adds value to an organization; it should be our goal,” comments Culwell.Risk management, security, loss prevention, whatever the label or title, there are things that chief security officers can do to win or keep his or her seat at the boardroom table and the confidence of the bosses and stakeholders. Metrics is one area. So are two other strategies: One is the effective selling of a security plan and the other is better management of the relationship of the CSO to C-suite executives.
There are cautions when it comes to metrics, however.
“How the CSO can effectively measure performance varies widely depending on which aspect of the program you examine,” suggests Imhoff.
But, “rarely will a broad survey of the general employee population yield valuable results,” Imhoff contends. “Most staff won’t know about many security services or, if they do, have a tangible sense of their value. If surveys are used, respondents must be those who are known to regularly interact with the service and understand its functions. They can only provide feedback in the context of that interaction. It’s important that responses are at or near the actual time of the usage experience. For instance, if only 10 percent of staff travel internationally, circulating surveys to all staff at large about international travel security management won’t provide meaningful feedback. Hearing from international travelers within days of a trip will provide value,” observes Imhoff.
Culwell takes a more focused view of metrics. “I’m of the belief that anything worth doing is measurable. Employees, customers and other department heads know good and poor security when they see them, and all should be given an opportunity to make their evaluations known. Surveys, especially 360-degree surveys, are an excellent tool to capture what others are thinking and/or recommending. Specific metrics such as reduction in the amount of thefts, unauthorized entries, unlocked vehicles and doors, as examples, are of value as well,” says Culwell.
Talk in C-suite Terms
When it comes to selling a security plan or major purchase to the boss, CSOs will gain by talking and proposing business benefits common to the C-suite focus, not security’s focus and lingo.Hatfield sees a two-step process when it comes to solid communications. “Security professionals need to understand the needs of each C-level executive and work to deliver the best security options. And security needs to be educated in communication to be able to address C level execs and have their points heard.”
“At all stages of a career you need to sell yourself, your ideas, your value, and your ability,” advises Patricia Fripp, who works with individuals from the C-suite, and is the author of Get What You Want!, Make It, So You Don’t Have to Fake It!
The back story of the Security magazine CEO Report Card 2010 is the need for enterprise security leaders to best manage the relationship with the boss, according to Jean Kelley, president and founder of Jean Kelley Leadership Consulting and who works extensively with corporate leaders.
Among her suggestions:
• Find out from your boss what “good” looks like and all who are involved in measuring “good” to make sure you’re meeting everyone’s expectations. After all, what seems good to you may only be mediocre to your boss.
• Ask the boss what kind of follow up he or she wants and what’s needed to meet the C-suite comfort level.
• Examine the boss’s style and adjust to that style. Peter Drucker says there are two key leadership styles: readers and listeners. The readers want data before you talk with them. The listeners want to talk before they read. And while there are many personality types in the workplace, if you can make this one distinction between the readers and the listeners, you’ll go far with managing the boss.
• Muster up the courage to tell the boss when you feel you haven’t been fully heard.
• Become aware of other managers’ styles, especially when they have a stake in the outcome of a project or plan.
The good news is that no matter how well or poorly security manages the boss’s relationship in the past, it can be re-crafted on every new project, adds Kelley. “Ideally, you want to create a relationship where talking from the heart is the norm, as then confrontation on serious issues won’t be difficult. In the end, it’s really about understanding your boss. When you teach your boss how to work with you and hone great communication skills with him or her, your work life will be happier and much more productive,” she stresses.
Among her suggestions:
• Find out from your boss what “good” looks like and all who are involved in measuring “good” to make sure you’re meeting everyone’s expectations. After all, what seems good to you may only be mediocre to your boss.
• Ask the boss what kind of follow up he or she wants and what’s needed to meet the C-suite comfort level.
• Examine the boss’s style and adjust to that style. Peter Drucker says there are two key leadership styles: readers and listeners. The readers want data before you talk with them. The listeners want to talk before they read. And while there are many personality types in the workplace, if you can make this one distinction between the readers and the listeners, you’ll go far with managing the boss.
• Muster up the courage to tell the boss when you feel you haven’t been fully heard.
• Become aware of other managers’ styles, especially when they have a stake in the outcome of a project or plan.
The good news is that no matter how well or poorly security manages the boss’s relationship in the past, it can be re-crafted on every new project, adds Kelley. “Ideally, you want to create a relationship where talking from the heart is the norm, as then confrontation on serious issues won’t be difficult. In the end, it’s really about understanding your boss. When you teach your boss how to work with you and hone great communication skills with him or her, your work life will be happier and much more productive,” she stresses.
A Routine of Meeting Expectations
Imhoff also emphasizes the importance of a strong relationship with C-suite executives. “There is no better way to communicate security’s value to the C-suite than to establish a routine that creates the expectation of essential information on a regular basis.”He adds, “It’s imperative these meetings and/or communications succinctly focus on key elements of security performance and highlight emerging issues with recommended, cost-effective solutions.
Internal security is not ordinarily a revenue center. Nonetheless, in the final analysis it has to be seen as productively enhancing the bottom line, else why have it. Depending on the nature of the business this takes many forms. For example, if quality client service demands a particular baseline of security attributes, such as protection of client data entrusted, then an effective access control system is an essential element when marketing services to these clients. It’s hard to prove a negative, but any client entering your space and coming away with an experience suggestive of lax access control probably is headed to your competitor.”
The line of communication is seen on the bottom line; security must add value to an organization, advises Culwell. “What ‘adding value’ means to an organization must be based on an understanding of the organization’s security needs, communicating those needs to executive management, and then following through. And, those needs will change over time; security professionals are nothing if not flexible. Crossing departmental lines, while sometimes tricky, is one example of adding value. Being customer service driven is the most obvious element of adding value. Finally, being able to define and defend a position against popular thought brings about credibility; nothing on this earth solidifies communication (and trust) better than credibility,” the City of Phoenix executive points out.
About the CEO Report Card
Surveys were sent to Fortune 1000 and other company CEOs, presidents, chief operating officers and chief financial officers with a promise to maintain confidentiality of responses. Companies had to have a staffed security department, operation or established staffer. The respondent companies range from $405 billion to $90 million in revenue, from 2.1 million employees to less than 500. Enterprises range from retail, manufacturing, financial and transportation to government, utilities, healthcare and educational institutions.
Selling Yourself and Your Ideas to the C-suite
Here are seven things to do and three things to avoid, according to Patricia Fripp, management consultant and author. The Fripp Do’s:1. Practice. A report to the C-suite is not a conversation; however, it must sound conversational. Once you have your notes, practice by speaking out loud to an associate, or when you are driving to work, or on the treadmill. Make sure you are familiar with what you intend to say. It is not about being perfect. It is about being personable.
2. Open with your conclusions. Don’t make the C level audience wait to find out why you are there.
3. Describe the benefits if your recommendation is adopted. Make these benefits seem vivid and obtainable.
4. Describe the costs, but frame them in a positive manner. If possible, show how not following your recommendation will cost even more.
5. List specifics, and keep on target. Wandering generalities will lose their interest. You must focus on the bottom line. Report on the deals, not the details.
6. Look everyone in the eye when you talk. You will be more persuasive and believable.
7. Be brief. The fewer words you can use to get your message across, the better. Jerry Seinfeld says, “I spend an hour taking an eight-word sentence and making it five.” That’s because he knows it would be funnier. In your case, shorter is more memorable and repeatable.
The three Fripp Don’ts:
1. Don’t try to memorize the whole presentation. Memorize your opening, key points, and conclusion. Practice enough so you can “forget it.” This helps retain your spontaneity.
2. Never, never read your lines — not from a script and not from PowerPoint slides. Your audience will go to sleep.
3. Don’t wave or hop. Don’t let nervousness (or enthusiasm) make you too animated — but don’t freeze. Don’t distract from your own message with unnecessary movement.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






