Logical Security
Special Report
Zinet Kemal | Women in Security 2024
Cloud Security Engineer — Best Buy
July 2, 2024
Special Report
Confidence Staveley | Women in Security 2024
Founder — CyberSafe Foundation
July 2, 2024
Special Report
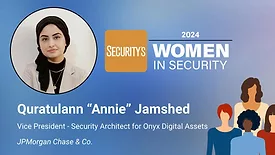
Quratulann "Annie" Jamshed | Women in Security 2024
Vice President - Security Architect for Onyx Digital Assets — JPMorgan Chase & Co.
July 2, 2024
Special Report
Dr. Iretioluwa Akerele | Women in Security 2024
Co-Founder — CyBlack
July 2, 2024
Special Report
Candice Frost | Women in Security 2024
Director, Integrated DoD Account — Nightwing
July 2, 2024
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing