Home » risk management
Articles Tagged with ''risk management''
The Rise of Extremism
The rapid growth of extremist groups provides many challenges for enterprise security.
June 8, 2020
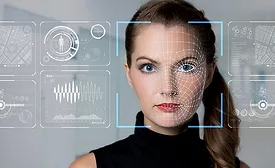
Continuous Monitoring of Employees Gaining Traction
Background checks are out; continuous monitoring is in.
June 5, 2020
Justin Dolly: Proven Security Leader
How Justin Dolly has demonstrated true security leadership over 23 years and what he brings to his CSO role at Sauce Labs
June 3, 2020
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing