The big takeaway from the Kaseya supply chain/ransomware cyberattack

This month, the world of enterprise security was badly shaken, as the Russia-based cybercriminal syndicate REvil launched yet another high-profile ransomware attack. The hackers, responsible for the recent attack on JBS Foods, infiltrated Kaseya VSA, an endpoint protection software solution used by large Managed Service Providers (MSPs). Through the software supply chain, REvil was able to quickly spread to at least 50 of Kaseya’s direct customers, with somewhere between 800 and 1500 small-to-medium sized businesses further down the supply chain.
This is not the first such attack, though it is REvil’s most ambitious (and successful) to date. Over the past year, we’ve endured SolarWinds, Colonial Pipeline, JBS Foods, and now Kaseya. This seemingly endless litany of supply chain-centric cyberattacks grows every week. As it does, companies and governments are simultaneously dealing with a host of other disruptions like COVID, the Suez Canal blockage, Brexit, international trade disputes, and more.
While these cyberattacks and global disruptors may appear dissimilar, having wildly varying causes and impacts, there is strategic value in considering them – and the supply chains they spread across – as a collective. Together, they represent a rapid learning opportunity for both adversaries and defenders – an open-source global weapons development program. The adversaries – hostile nation states and cyber criminals – are already studying these elements for future tweaks toward enhanced weaponization. So should we.
What have they learned?
Every supply chain disruption – be it a successful hack, a natural disaster, or an international political dispute – increases the information adversaries and defenders have on the effectiveness of techniques, viability of targets, and the favorability of global circumstances. All of which can be mixed and matched, refined over time to discover not just the ideal avenue for an attack, but the optimal conditions of the greater supply chain and business ecosystem under which to conduct one.
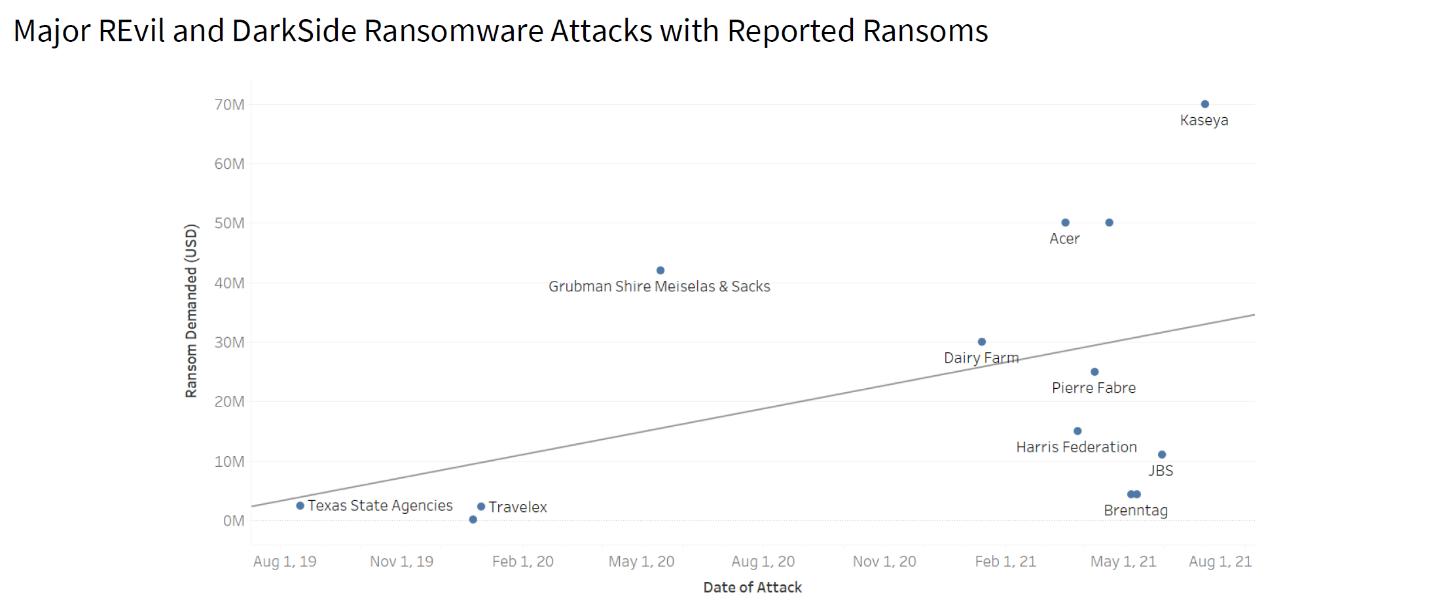
Major Revil and DarkSide Ransomware Attacks
What everyone is learning is that the battlefield we’re on is considerably larger than previously imagined. We’re used to thinking about the enterprise as a collection of endpoints that need securing. The effectiveness of these supply chain shocks shows that our enterprises are also individual nodes of a much bigger macro-network. It’s a battlefield so large that drawing up a strategic defense using conventional tools and tactics won’t work. To do so effectively, we need to learn about this broader playing field in all of its dimensions – from enterprise networks to transportation/logistics tools to environmental and labor concerns.
Understanding the interplay between these elements is crucial. In addition to the direct damage done to Kaseya, this latest attack shut down 800 supermarket locations that could no longer operate their checkout software, interrupted Swedish rail service, and disrupted the operations of a Swedish pharmacy chain. A more holistic understanding of the possible knock-on effects of a cyberattack could have enabled defenders to better prepare for the situation or, at the very least, understand the level of digital concentration risk posed by having so many critical systems in one country connected to a single application.
Attacks like the recent strike on Kaseya have upended how we think about crime. Conventionally, attackers strike on a single target, and receive payment from that target. Today, attackers are essentially able to, using the supply chain, probe endlessly for small fissures in our digital armor, and strike many victims simultaneously, while collecting untraceable ransoms in an endless variety of cryptocurrencies.
Nested networks
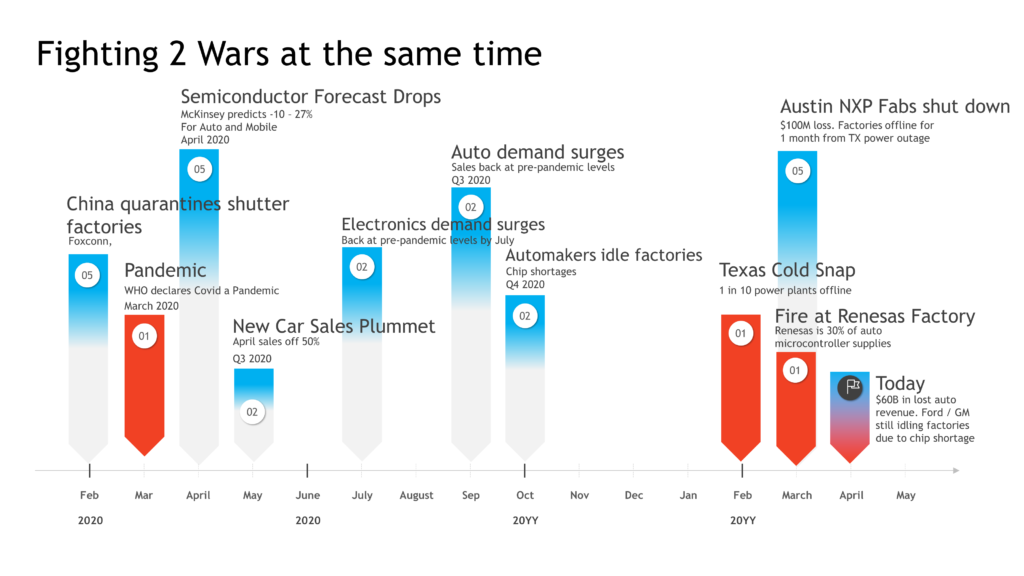
This is a problem of networks within networks. Consider the ongoing supply chain disruption facing the semiconductor industry. On the surface it’s a simple matter of demand exceeding supply. But when you examine it from a more holistic, networks-within-networks perspective, it becomes infinitely more complex.
An expected, COVID-driven dip in automotive sales led to a reallocation in silicon production resources. When that dip failed to materialize at the same time as a spike in consumer electronics purchasing, combined with a litany of natural disasters affecting production: the great silicon squeeze was on. This representation is, of course, still greatly simplified from the reality of the situation, which involves thousands of companies, millions of workers, and impacts practically every person on this planet.
With a holistic understanding of multi-factor supply chain risk — how the non-obvious connections and dependencies were poised to amplify this shortage — we could have limited the impact, or strategically allocated resources. This problem of understanding exposure and how the supply chain can magnify small disruptions into massive ones, lies at the heart of the ransomware challenge as well. If we are to have a hope of preventing supply chain-based cyberattacks, understanding their potential impact, and mitigating the proliferated “fan-out” damage when they occur, we need to understand the entire picture.
The supply chain challenge
Kaseya is, in many ways, a microcosm of the entire problem. MSPs relay on the convenience of tools like Kaseya VSA to easily connect and deploy software across complex ecosystems. This interconnectivity creates convenience but also magnifies the potential impact of a single attack. This is also true of the broader global supply chain, where the closeness created by globalization similarly magnifies the potential impact of any one supply chain disruption.
Both of these problems, the security concern and the greater, global supply chain problem, reflect the same fundamental security challenge: defending a network or system with countless endpoints on the edge requires centralization of defensive resources; but that centralization inherently creates ideal attack points that, when compromised, immediately create massive risk to the entire system.
What’s more, both the Kesaya and SolarWinds attacks, though hugely impactful to a handful of customers and industries, are almost insignificant when compared to the potential impact of a similar compromise to one of the truly universal software providers. Imagine the situation if Amazon, Microsoft, Apple, or Google were similarly compromised. These organizations regularly push updates that affect the virtual entirety of consumer and enterprise computing resources on the planet. Their respective cybersecurity measures are obviously among the most stringent on the planet, certainly for the private sector — but still the point is made.
To have a hope of blunting the inevitable impact of such a potentially devastating attack, security leaders, company C-suite leadership, and governments need to stop looking at the problem in isolation and begin considering the broader context. We must implement comprehensive, multi-tier, multi-factor, continuous risk monitoring across the entire supply chain if we are to understand how and where we are most vulnerable, and where to concentrate defensive resources. The goal is not only to survive these constant attacks, but to thrive in spite of them.
*All images courtesy of Interos
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!