Culture First, Technology Third

As a Security Risk Management Services (SRMS) provider, we understand that most security programs will be underleveraged or undervalued if there is not an assessment of the organization’s culture.
The bottom line: Culture is another way of saying “This is how we do things around here.” In most cases, what is written down or hung on the wall does not align with “how we do things around here.” People will perform their roles, work within their processes and utilize technology to get things done; but the values that undergird their behavior and the ability to understand them and leverage them is one of the keys to unlocking the value of security.
We know from the subject matter experts in the industry that there are tools that can be leveraged to self-assess as well as form the basis for a collaboration with a consulting firm that has a practice in organizational change management.
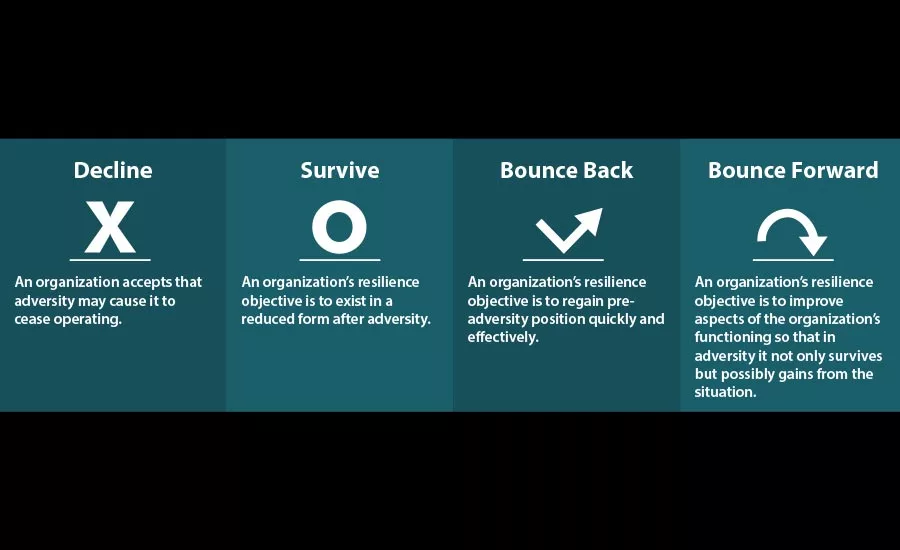
One self-assess tool is on the Australian Government’s Organizational Resilience website. Thank you to Ray Bernard, one of the best security minds in the industry, for referring us to the site: www.organisationalresilience.gov.au. This graphic from the site (above) is a compelling reminder of the leverage the culture has in the outcome from a serious event.
However, the culture also can be used proactively to provide a force multiplier in the reach and practice of mitigating risk. By asking questions, such as the ones on the Australian Government’s site, we have the means to engage risk owners inside the culture. Security has a way to open the door of the risk owner and open their minds to their risk and their opportunity. Security can be a business optimizer and value generator. The keys to this are in the core operational processes of the organization led by these ‘‘risk’’ owners. We must become students of their core processes and their measures of performance.
Once this is done, we can begin to build on a sense of urgency driven by these core operating principles. We like to say: “The business of security is the business.” The value of the security program’s investments is the direct result of measuring the impact of risk and opportunity. You cannot leverage this or understand it until you truly understand it through a full program assessment.
Once you have the data, then you can begin to leverage the principles of organizational change management to guide the strategy, planning and measures of performance. The risk owners will help fund the security program based on the data they perceive and understand.
We have seen this powerfully unfold in such diverse markets such as data centers, software companies and healthcare. So, we know it transcends industries and business models.
We hope to see more security leaders combine a culture assessment, risk assessment and a technology assessment before spending time and money on implementing more technology. Technology has its place. It can be a powerful optimizer of core processes including situational awareness and actionable response. However, its value is multiplied commensurate with having a 360-degree view of risk and opportunity or, in other words, the business. Technology vendors (manufacturers), integrators and consultants should be proud and thrilled to support a ‘‘path to value’’ for the client that anchors their value and future.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!









