Access Control -- Vehicle Theft
Chicago Thieves Crack Vehicle Security Codes
Jupiterimages / PHOTOS.com>> / Getty Images Plus / Via Getty Images
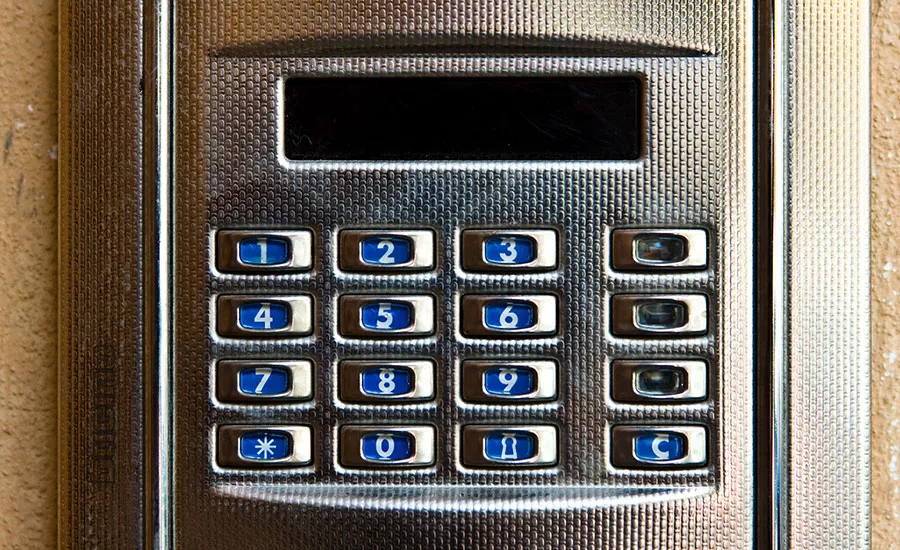
Cars in Chicago are being broken into without thieves having to break anything except the security codes used to open the electronic doors, according to an article from ABC News.
Home video surveillance caught a man walking past a car on a downtown, residential Chicago street, when the car’s dome light came on. At that point, the man opened the door, sat down and left moments later with belongings that had been inside the locked car, the article reports.
The car shows no sign of forced entry, baffling victims of these crimes – many of whom simply believe they forgot to lock their car doors.
According to ABC, wireless signal experts think some car thieves have cracked security code so they can send the same signal that an owner’s key transmitter sends.
“We believe that this code-grabbing technology was utilized and we are looking into it and investigating,” says Chicago Police Department’s Andrew Schoeff in the article.
Keyless entry system technology has become more complicated since 2010, and now car security codes change on a regular basis. However, cars built before that period are a different story.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





