Secure Card Supplies: Not the Average Accessories

High performance card printers also need high performance accessories and supplies.
When you buy a high performance car, you expect to use high performance supplies and parts with it in order to get the best results. That same approach applies for a high performance, high security printer. The security of the cards you print depends on the quality of the supplies used in the process. When cards are used for authentication and authorization in access control and identity programs, it is critical that organizations use premium, security-focused supplies.
Several new counterfeit-resistant cards, protective laminates and printer supplies are now available on the market. These supplies are optimized for best printer performance and offer maximum reliability and security.
To help prevent fraudulent card reproduction via photography or photocopying, new security-focused supplies provide customers with better choices for personal identification applications requiring additional security or protection of cards. Options include customizable security cards with embedded holograms, opacity marks, micro text, nano text and UV text.
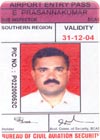
Finely printed detailed graphics in the header and behind the photograph make this card extremely difficult to duplicate.
Innovative Printer Supplies
Security conscious organizations should consider the following when reviewing its card-printing program.Embedded Hologram Cards – It’s now possible to implant a tamper-resistant hologram within the layers of plastic cards for added low-cost security. This feature is part of the inner layer of the card and cannot be scratched off or removed. The hologram incorporates a visible and ultraviolet pattern or logo that becomes part of the background of the white card, allowing printing and laminate to be applied directly on top of the hologram.
Opacity Marked Cards – These cards also provide a tamper-resistant printed image within the layers of a plastic card. This printed image acts as a watermark, only visible when held directly in front of a bright light source. With color-shifting ink cards, a single image changes from one color to another, adding yet another layer of security. This feature, too, is part of the inner layer of the card and cannot be scratched off or removed.
Pre-printed Text – Card supplies can be custom ordered with pre-printed text that can only be read with magnification or UV exposure. This makes the cards very difficult to duplicate or photocopy, resulting in a higher level of security. Options include pre-printed micro text, nano text or UV text. Ultraviolet visible text and graphics are available in two colors, green and blue. With micro printing, text can be added to a user’s specifications, with deliberate random font changes and misspellings if desired. Character height is 5 thousandths of an inch (0.125mm). Laser etching is another option. The inner surface of the laminate can also be pre-printed with OVI ink or UV-visible ink in one, two or three colors.
Pre-printed Serial Numbers – Card serialization can also be incorporated into card stock, adding yet another security dimension. Printers with a magnetic stripe encoder, proximity encoder or smart card contact options can be set up to function only with serial numbered card stock. With card serialization, all cards supplied to an organization using this system are pre-printed on the front or back with a serial number, which is also recorded on the card’s credential medium, such as magnetic stripe, proximity chip or smart card integrated circuit. The ID card printer is configured to accept only serial numbered cards and will eject (without printing) any card without the appropriate encoding. If a valid serial number is detected, the card is printed in the usual way.
Protective Laminate Ribbons – Protective laminate ribbons are now available for security-focused printers. These printers can automatically apply a thick protective laminate to cards. The protective material is applied directly to the card to prolong the life of the printed image by shielding it from UV light (fading of image), preventing dye-migration, and reducing normal wear from handling and frequent swiping of cards through magnetic stripe readers. The laminate can also provide an additional level of security by adding unique and customizable holograms.
Hand-applied, Peel-and-Stick Laminates – These laminates come in pre-sized patches that are easily applied to printed cards, providing additional security for low-volume applications.
RFID Technology – A printer with RFID (radio frequency identification) technology takes both simplicity and security a step further. Intelligent printing systems incorporate RFID technology that minimizes the need for user intervention. For example, RFID enables automatic driver configuration, automatic ribbon type detection, enhanced image quality, “load and go” operation, ribbon low notification and more accurate color printing. The RFID technology also ensures that only authorized material can be used in the printer. Printers are configured to reject any ribbon that does not have a specific RFID-tagged ribbon installed.
Secure Supplies Now
A growing number of government agencies and corporations around the world rely on in-house card printers for demanding, high-security applications, including the production of identification badges and millions of driver’s licenses each year. It is critical for these organizations to use supplies that create more highly secure cards. New products that are now on the market can help meet this need.Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




