Security Enterprise Services
Leadership & Management
Finding your volunteer leadership lane
As security leaders, there are a number of opportunities to lead within and outside of our own organizations.
March 15, 2023
Career Intelligence
The challenge of ghost jobs
Security professionals on the hunt for new roles should be cautious of job postings that are less reputable than they appear.
March 13, 2023
Security Strategy
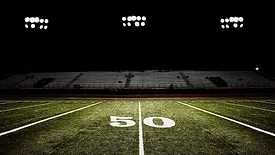
Keeping stadiums secure despite staffing shortages
A number of security strategies and technologies can help stadium operators ensure the safety of their events.
March 8, 2023
Product Spotlight
ISC West 2023 product preview
From robotic visitor management to mobile access control credentials, Security magazine spotlights solutions from companies at ISC West 2023.
March 6, 2023
Enterprise Services
Mitigating emerging security risks
Determining, prioritizing and mitigating developing risks takes planning, networking, understanding, education and patience.
March 6, 2023
Special Report
Security's 2023 Top Cybersecurity Leaders
These cybersecurity professionals bolster global information security initiatives through their dedication, influence and passion.
March 1, 2023
Special Report
Phillimon Zongo - Top Cybersecurity Leaders 2023
Co-Founder and CEO, Cyber Leadership Institute
March 1, 2023
Special Report
Ariel Weintraub - Top Cybersecurity Leaders 2023
Head of Enterprise Cyber Security, MassMutual
March 1, 2023
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing