How Dependence Can Ruin A Supply Chain
The economic horizon was showing signs of new life and your business-improving Orders were up, but you have concerns that you have stretched the length of your supply chain
|
The economic horizon was showing signs of new life and your business-improving Orders were up, but you have concerns that you have stretched the length of your supply chain halfway around the world. The news caught your attention with an alert . . . a major earthquake had just hit Japan and the expected tsunami was predicted to cause even greater devastation. Your heart sank thinking about the loss of lives and the human suffering that follows such a major natural disaster. Then it hit you…your most important single-source key supplier was located right in the center of the worst hit area. For many years, procurement organizations have been driven to extract the best pricing from suppliers. Companies have focused relentlessly on reducing costs. Many large corporations require suppliers to produce annual cost reductions or risk being replaced by a competitor somewhere else in the world that is more than willing to produce the required product at the required cost savings.
Sole sourcing of a component, sub-assembly or complete product from a key supplier is a concession that many companies make to obtain the best possible pricing. Few companies place sufficient weight on the ramifications supply chain disruptions can create when making sole sourcing decisions.
If you want to do a quick gauge of your supply chain and logistics network risk, take a look at the performance plans of procurement personnel and the performance metrics of the overall procurement organization. In all probability, their performance plans will focus on cost reductions, and the metrics upon which the organization is measured probably won’t have a single mention of measuring risk.
Many companies learned a very hard lesson from the events that unfolded after the devastating earthquake, tsunami and nuclear disaster in Japan. Many key suppliers in Japan had their factories severely damaged or destroyed. A number were located in an area that had been determined to be in a nuclear hazard zone and were prohibited from shipping product out of that area. As a result, many assembly lines around the world ground to a halt.
While the events in Japan taught us the downside of over-stretched supply chains and sole-source risks, many similar (too late) lessons-learned about disruptions and other foreseeable impacts to supply chains and logistics networks could have been avoided.
Companies have also learned hard lessons about the fragile nature of excessive dependence on logistics networks delivering key parts or sub-assemblies to final assembly facilities or finished product to market. Logistic network delays are costly and can be extremely disruptive to manufacturing planning cycles. The U.S. implemented the Customs-Trade Partnership Against Terrorism (C-TPAT) program in an effort to help companies speed deliveries through ports. While this has been a very successful program overall, other issues continue to plague logistics networks. Dock worker strikes, pirates, cargo theft and a host of other events impact the reliability and stability of logistics networks. The more complex and far-reaching your logistics network is the greater your risk of disruption.
Few companies conduct the kind of in-depth due diligence that is necessary to effectively screen supply chain and logistic network partners. In today’s world of increasing regulation and government oversight, effective due diligence is not only a smart thing to do, but it is necessary to avoid the regulatory or legal liability quicksand of what will, in all likelihood, be deemed avoidable or foreseeable. Knowing as much about whom you are doing business with is a vital part of managing your risks with suppliers and logistics network partners. Any past or potential FCPA violations; non-compliance with conflict material regulations; export control violations; conducting business in countries under embargo or sanctions; relationships with known terrorists or entities connected to organized crime enterprises by your supply chain or logistics partners, can and in all probability will, become your company’s problem…and liability.
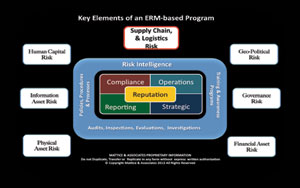
Developing a structured process of supply chain and logistic network risk assessments is vital to ensuring to the greatest extent possible that disruptions will be minimized. As part of that assessment process, effective due-diligence of entities with whom you partner is critical to not only defending your competitive position in the marketplace, but to safeguarding your enterprise’s brand and reputation.
About the Authors:
Jerry J. Brennan is the founder and Chief Operating Officer of Security Management Resources (SMR Group), the world’s leading executive search firm exclusively focused in corporate security. Lynn Mattice is Managing Director of Mattice and Associates, a management consultancy focused at the development and alignment of Enterprise Risk Management and Business Intelligence Programs, as well as Intellectual Property Protection and Cybersecurity.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








