Product Spotlight: Social Media Monitoring Solutions
Facebook, Twitter, Instagram, YikYak, Weibo…. There are dozens, if not hundreds, of different social media platforms on the market today, and maintaining a grasp of your enterprise’s reputation and any potential risks in your area can be a challenge.
Identify Trends Behind Social Media Posts
Identify Trends Behind Social Media Posts
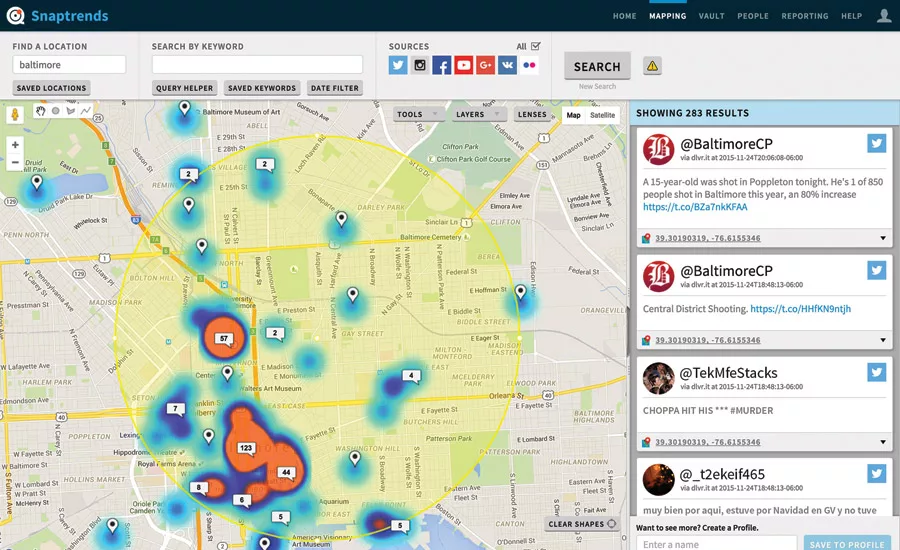
The “Geosocial Intelligence” SaaS solution from Snaptrends empowers enterprises to better understand social media trends and conversations within the context of location, enabling stakeholders to make more informed decisions. Users can monitor a single facility or multiple locations worldwide, and searches can be filtered by keyword, location, user or social platform. The “automated discovery” feature enables users to learn of threatening trends and sentiments about the company from customers and employees.
Learn more at snaptrends.com
Creates “Geofence” for Location-Based Detection
Creates “Geofence” for Location-Based Detection
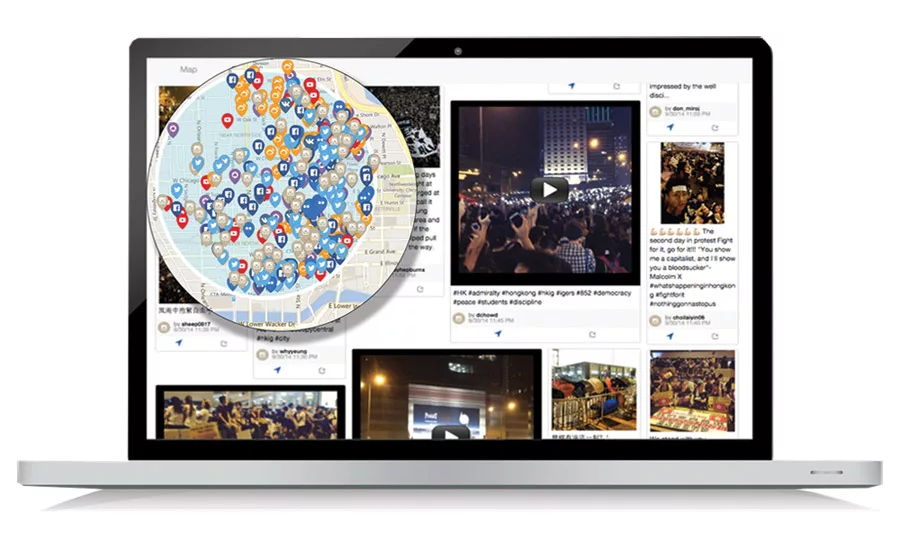
Web-based application Geofeedia is a location-based social media intelligence platform for security and risk management. The program allows enterprise security leaders to create a “geofence” around a location of interest and view posts (images and text) from across social networks coming from that area, in real time or historically. Geofeedia can also detect the sentiment behind posts, which can help predict future events. The platform enhances corporate intelligence-gathering by identifying social media trends in areas that matter in order to better protect assets, facilities and employees.
Learn more at geofeedia.com
Distills 500 Million Tweets per Day into Valuable Signals
Distills 500 Million Tweets per Day into Valuable Signals
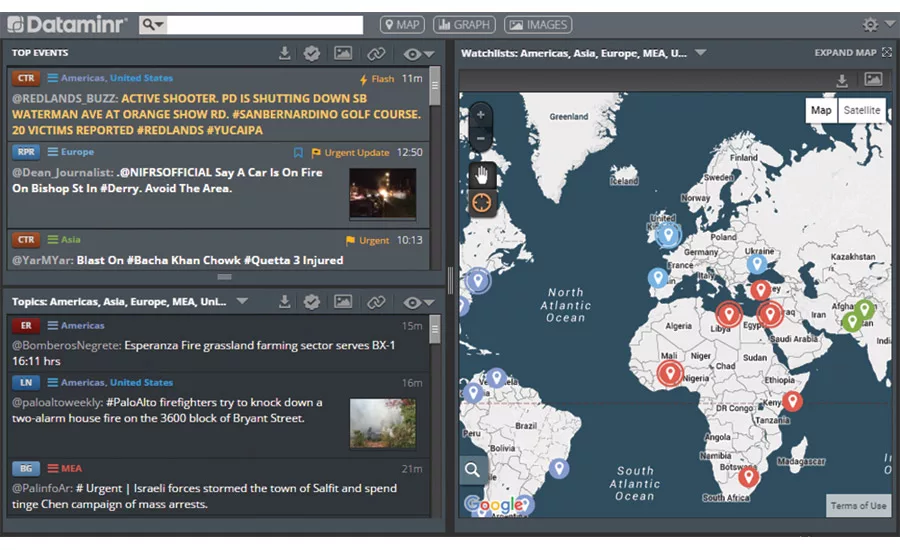
The real-time information discovery platform from Dataminr sifts through all public Twitter posts to find those that are most relevant to your company, classifying them based on geo-location, topic relevancy, and market moving implications, then ranks them based on the level of urgency. The signals are delivered via a Web browser, instant messenger, email, mobile app, or can be integrated into the security workflow. The system provides transparency into sources’ credibility by tagging them as reporters or emergency responders, for example, compared to general chatter.
Learn more at www.dataminr.com
Alert, Assess, Act
Alert, Assess, Act
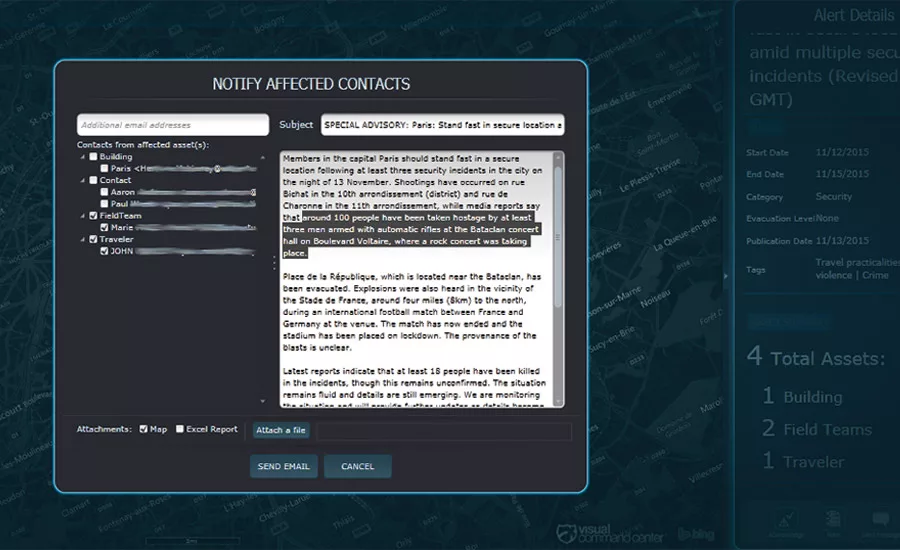
The Visual Command Center from IDV Solutions is based around “Alert, Assess and Act.” The VCC brings together information and capabilities from disparate external and internal sources to provide a real-time, common operating picture of an enterprise’s personnel, operations and assets in relation to potential threats to those assets. In the event of the November 2015 Paris terrorist attacks, for example, the platform would send an automatic alert because of a risk located near a company’s assets, followed up by connecting the user to external and internal information sources, showing a summary of the people or assets nearby and social media posts about incidents in the area. Then the enterprise could notify its users in the area with an overview of the situation, and the system can ask if they are safe, provide instructions or maps to safety.
Learn more at www.idvsolutions.com
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing