People: The missing piece of the insider threat puzzle
Incorporating social and behavioral science in insider threat detection

Image via Freepik
Organizations have historically protected their infrastructure from adversaries by spending billions each year on singularly focused, cyber-centric reactive technology defenses. Similarly, the focus on resolving insider threat events has historically zeroed in on implementing defenses focused on network anomalies and addressing lax security protocols and information siloes within organizations.
Traditional defensive and remediation efforts only take us so far. They are proving to be ineffective and inefficient, as evidenced by an increase of 47% in security incidents with an insider threat nexus between 2018 and 2020. So, what’s missing? These efforts largely — if not completely — focus on the tech and ignore the people.
The making of an insider results from the complex interchange between individual, social, and organizational factors, and people are the common denominator. Despite top-of-the-line cyber defenses, extensive vetting, and monitoring, trusted insiders exfiltrate secrets, hack systems, and find themselves caught in the traps of adversaries.
Simply put, insider threat is a people problem, and we can no longer afford to deprioritize or discount the human factor in insider threat detection and remediation.
The Critical Pathway to Insider Risk
Edward Snowden. Robert Hansen. Aldrich Ames. Anna Montes. Nidal Hasan. What do they all have in common? Each weaponized the trusted access and placement they held in organizations and became poster children for insider threats; however, each person’s pathway to becoming an insider was distinctly different.
There are no one-size-fits-all behavioral profiles practitioners can use to identify or proactively detect insiders because no single typology of person becomes an insider, and no singular set of circumstances facilitates a malicious act.
Despite taking different paths, history and empirical research tell us that those who become insiders follow a rather predictable and critical pathway. Over the last 20 years, The Critical Pathway to Insider Risk (CPIR) has served as the leading multifactorial framework that takes common behavioral indicators and precipitating events into account, operationalizing the amalgam of factors into an index of risk for insiders.
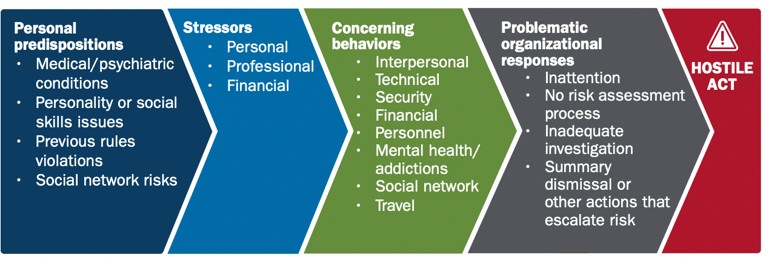
Image courtesy of The Cybersecurity and Infrastructure Security Agency (CISA)
Person-in Environment
Popular culture has brought us wildly successful series like Criminal Minds and Mindhunter, introducing the world of the Federal Bureau of Investigation’s (FBI) ‘Criminal Profiler’ to audiences and bringing to the forefront the FBI’s strategic use of social and behavioral sciences to identify and capture violent criminals.
While you may not be hopping on a G5 and jetting across the country to hunt a serial killer as the fictional FBI squad does in Criminal Minds, incorporating social and behavioral sciences in your approach to mitigate the risk of insider threats to an organization is becoming a necessity. The focus cannot solely be on cyber-data and threats from nation states and need to equally narrow in on people and their pathway to becoming an insider. Social and behavioral sciences (SBS) are well positioned to address the complex and persistent human factor of insider threats so that organizations can start to be more proactive vs. reactive.
Unlike when catching a serial killer, demographic profiles provide little insight when it comes to proactively detecting insiders because spies, hackers and malicious insiders come in all shapes and sizes, ranging in age, education level, race, gender, etc. Using a person-in-environment approach to analyze behavior is most effective to understanding an individual and their behavior — how they see the world, how they think, how they respond to others.
The Individual
Nearly 90% of Security leaders assert the necessity of using personal indicators and behaviors to identify high-risk insiders.
Individual attributes inform and baseline one’s behaviors and activities and the ways in which an employee interacts with their organization or its network. These behaviors are directly observable by others, and changes in them can be considered a threat indicator.
Biological and psychological factors and attributes — ranging from psychiatric disorders influencing self-control and judgment to narcissism, psychopathy, and/or a history of violent behavior(s) — increase the likelihood of someone becoming an insider. When combined with personal issues like financial distress, addiction, relationship changes (i.e., divorce) and unmet expectations, responsibility changes, compensation and/or recognition at work, these markers serve as predispositional person-specific indicators of possible insider behavior.
Due to the sensitive and incredibly personal nature of this threat indicator, organizations must comply with all privacy, labor and employment statutes, policies, rules, and regulations when exploring individual, behavioral-based indicators.
The Environment
Insider threats occur in a social context. Bottomline, organizational policies, cultural practice and cultural awareness within organizations matter. The pathway to one becoming an insider is not solely determined by individual choices, stressors and/or predispositions. The relationship one has with their environment has the potential to create an insider threat.
High-stress workplaces riddled with toxic, overly aggressive leadership who tolerate poor performance, and show no appreciation for employees, create additional motivation for a once trusted insider to become a risk to an organization.
In fact, a 2022 report from Palo Alto Networks and Unit 42 identified that around 75% of insider threat cases involved a disgruntled former employee who stole, destroyed, or improperly accessed data and/or networks.
Building a Trusted Workforce
Understanding how someone chose the insider threat path allows practitioners to better anticipate future threats and get in front of existing ones.
While we cannot predict human behavior with 100% certainty, approaching insider threat mitigation with a person-in-environment lens, combined with tried-and-true cyber indicators, only enhances an organization’s insider threat efforts.
Continuous evaluation and scoring of these combined factors — technical, human behavioral and social — are key to establishing structured and supported intervention points, allowing an organization to build and maintain a trusted workforce and ultimately stay ‘left of boom.’
The views and opinions expressed are that of the author and not those of the FBI or any other U.S. government agency.
This article originally ran in Security, a twice-monthly security-focused eNewsletter for security end users, brought to you by Security magazine. Subscribe here.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






