Small-to-Medium-Sized Enterprises More Likely to Adopt Cyber Insurance

Cowbell Cyber, company which maps insurable threats and risk exposures using artificial intelligence to determine the probability of threats and impact on coverage types, released “The Economic Impact of Cyber Insurance,” a survey analysis focused on cyber insurance for SMEs. The Cowbell Cyber analysis is an extension of “Driving Cybersecurity Performance” — a research report published by ESI Thoughtlab — and specifically extracts data for cyber insurance buying intentions, drivers, satisfaction, limits, and disparities between SMEs (revenue <$1B) vs. large enterprises (revenue >$1B) in the United States.
Respondents had responsibility for cybersecurity or detailed knowledge of its use. More than 9 in 10 were C-level executives. The survey examined cybersecurity investments, plans, practices, and performance results at their firms. It included quantitative questions to allow ESI ThoughtLab economists to develop a rigorous cybersecurity maturity framework, analyze performance metrics, benchmark practices, and measure the ROI on cybersecurity investments.
According to the ESI Thoughtlab report, which surveyed executives at 1,009 companies across 13 industries from November 2019 to January 2020, 65 percent of SMEs are planning to spend more on cyber insurance as part of their cyber resilience plan in the next two years, compared to 58 percent of large companies.
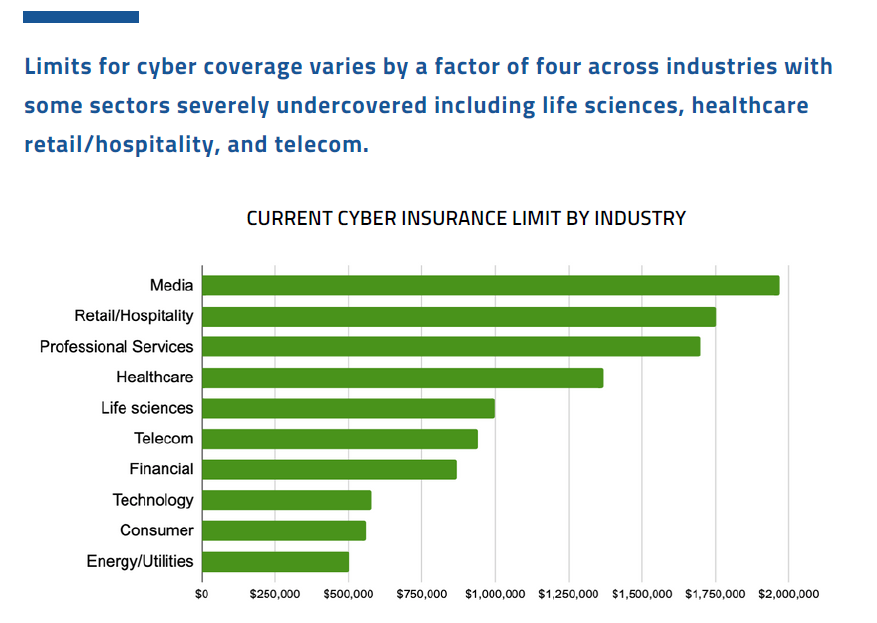
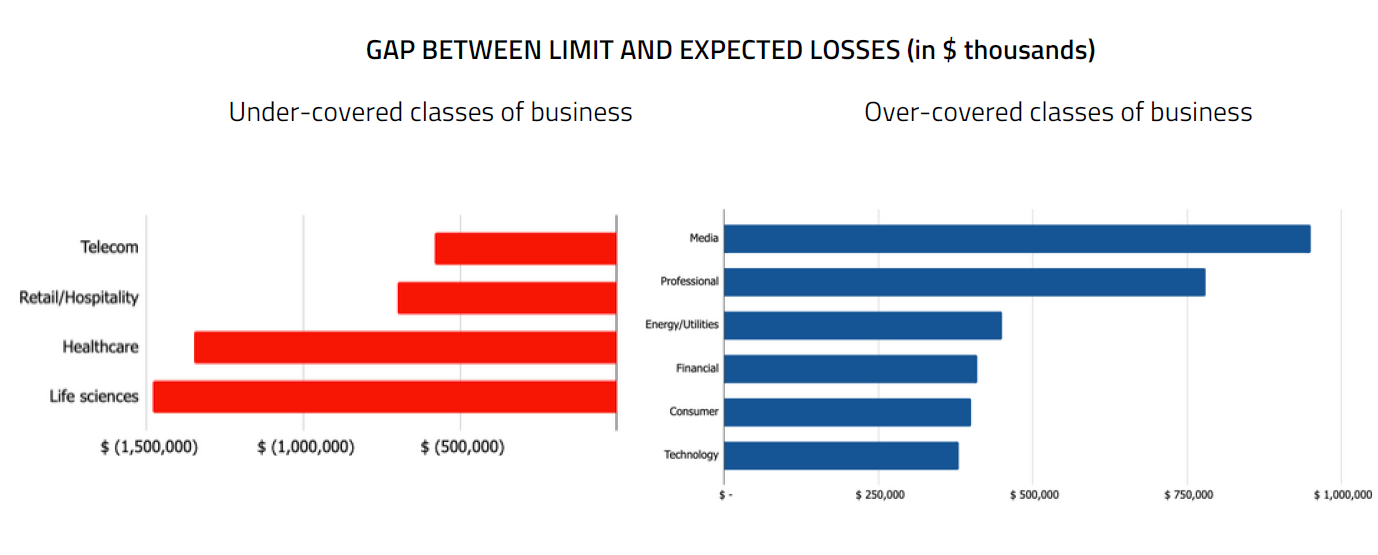
The report also finds that 71 percent of SMEs have a cyber coverage limit lower than $1M and lower than total past or estimated future losses and expenses related to a cyberattack. Further, cyber coverage limits varied across industries, with the report finding that life sciences, healthcare, retail/hospitality, and telecom are severely under-covered and show the biggest gap between limit and expected losses.
“Cyber breaches are no longer an ‘if’ scenario but rather a ‘when’ scenario. Our analysis of the survey results show that cyber insurance is becoming increasingly popular for SME organizations that want to protect their assets and accelerate the response and recovery process in the aftermath of a cyber incident,” said Isabelle Dumont, VP of Market Engagement at Cowbell Cyber. “Cyber insurance is now a necessity and not a luxury for organizations."
Additional key takeaways from the analysis report include:
- SMEs and large enterprises converge on the likelihood of their business experiencing a breach over the next year: 45 percent
- 62 percent of SMEs in the early stages of cybersecurity maturity believe that cyber insurance is well worth the protection. Only 13 percent said cyber insurance was not worth the protection it affords.
- On average, organizations opt for cybersecurity insurance coverage limits of about 0.14% of revenue
- Cyberattacks using password and credential reuse cause the greatest losses today and the greatest risk over the next two years
- Multi-Factor Authentication (MFA) is significantly under-deployed in SMEs (18 percent) compared to very large enterprises (43 percent)
- 55 percent of SMEs point to employee-owned end-user devices as the highest risk in two years
- 35 percent of SMEs buy cyber insurance because it is a customer requirement, and 30 percent of SMEs buy insurance because of regulations requiring restitution to individuals/third parties
- SMEs show less confidence than larger ones in their people, processes or technology investments to reduce the probability of a breach.
To download Cowbell Cyber’s cyber insurance survey analysis please visit here. To obtain access to ESI Thoughtlab’s research report, please visit here. SMEs can sign up at https://cowbell.insure/for-businesses/ to access a free comprehensive security risk assessment.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





