The Security 500: Beyond Best Practice to Best Fit



Click here to view the Security 500 Rankings |
Click here to view the Security 500 Sectors |
For years, enterprise security executives have been sharing “best practices.” In fact, that’s one of the missions of this publication: to provide peer to peer knowledge and sharing of information to effectively and successfully run an enterprise security and risk management program.
But is it time to tweak that “best practice” verbiage? Is it time for a change?
That’s not to say that sharing experience isn’t a good thing. Of course it is. Relationships in business, especially in enterprise security, are key. I’ve heard from so many of you who have shared not only metrics, but incidents, theories and more, with your colleagues. That should never change, and we want to continue to promote and help you to communicate them.
So why share “good practices” versus “best”? Well, if something is a best practice, then every other practice is inferior. But if everyone is doing the same best practice, it leads to conformity. And while a handful of best practices might be applicable universally, what’s considered a best practice in one industry, company, country or corporate culture isn’t necessarily a best practice in another. Can the best practice even be transferred or does it require modification? If it is modified, is it still a best practice?
A best practice implies accumulating and applying knowledge about what is working and not working in different situations and contexts, including lessons learned and the continuing process of learning, feedback, reflection and analysis.
Perhaps the most important thing to focus on is what works for an enterprise based on internal rather than external analysis. This means determining the “best fit” and alignment for each individual company given its unique needs, culture and business circumstances. By focusing internally, enterprise security can create overall good and solid practices that are relevant and add value.
Increasingly, we are hearing more application of “good practices,” which involves aligning to the extent possible with a methodology that is generally works in most situations. Good practice documents may include guidelines, metrics codes of practice, procedures manuals, regulations and other documents, as is the case in other industries.
A Good Practice is the here and now and is adaptable to the enterprise and its environment. A Best Practice is something that is generally only in the eyes of the beholder.
Perhaps you are already doing this. If so, I’d like to know. Please email me your comments, ritcheyd@bnpmedia.com. I’d be happy to compile them and share with all of our readers.
As we compiled this year’s Security 500 Top 10 Trends based off of your input from the Security 500 Survey, we hope to offer a few good practices of our own, supplemented by the conversations we’ve ha d with you, our readers, throughout our more than 50-year publishing history.
2016 Trends
1. Workplace Violence and Active Shooter
6. Asset Protection, Theft and Investigations
7. Training and Employee Hiring and Retention
8. Technology and Contract Management and Maintenance
9. Executive and Employee Travel
1. Workplace Violence and Active Shooter
This year, Security 500 members rated workplace violence and active shooter as the top number one threat facing an enterprise and its security team.
Workplace violence specialists suggest that the increase in workplace violence deaths “reflects the growing anxieties among employees as wages stagnate, living costs rise, and on-the-job pressures intensify from companies operating with leaner staffs,” the Houston Chronicle reported.
Overall, two million workers a year are affected by some form of workplace violence, according to OSHA, which includes everything from verbal abuse to physical assaults to homicide.
About 700 people a year are murdered on the job. The most extreme types of violence result in fatalities. Between 1992 and 2012, there were 14,770 workplace homicide victims, or roughly 700 a year on average, according to federal government statistics.
Shootings account for the lion’s share of those. Gun violence resulted in 78 percent of the workplace homicides in 2010.
But workplace violence isn’t always about work. In two-thirds of workplace homicides, the assailant has no known personal relationship with the victims, according to the Bureau of Labor Statistics. Then there are instances where a victim of domestic violence may be attacked by an abusive partner at work.
Injury to healthcare providers once was culturally accepted as “part of the job” given that the rate of assault is high in the profession. Some 75 percent of the 26,000 significant injuries from workplace violence occurred in healthcare and social services sectors, the Bureau of Labor Statistics reported in 2013.
One good practice comes from Jim Sawyer, Director of Security Services for Seattle Children’s Hospital. When it comes to workplace violence, Sawyer strives for a “zero incidents” rather than a “zero tolerance” approach to security.
“The finest violence prevention program on the planet in the workplace is optimum, caring, empathetic and aware customer service. It is more important than camera systems, biometrics, locks, batons, TV – it is the ultimate foundation for your zero incident or violence prevention program,” says Sawyer. “The most important thing for security people is making a good first impression, because how you stand, talk, act, interact with someone impacts directly with how they stand, talk, act, interact with you.”
2. Cybersecurity
Security 500 members rated cybersecurity as the second threat facing an enterprise and its security team, down from number one last year, even though only 35 percent reported having direct responsibility for it.
Findings from an annual Ponemon study on data breaches showed that while more companies have plans in place, they still lack confidence and are failing to take crucial steps as part of the preparedness process, preventing them from being truly ready for a real life data breach incident.
Another recent study revealed that nearly 65 percent of cybersecurity professionals struggle to define their career paths. The study by the Information Systems Security Association (ISSA) and independent industry analyst firm Enterprise Strategy Group (ESG) found two big “red flags:” The majority of cybersecurity professionals aren’t receiving the right level of skills development to address the rapidly evolving threat landscape. And the skills shortage has created a job market that represents an existential threat, adding job-related stress to cybersecurity personnel while making it harder for organizations to protect critical IT assets.
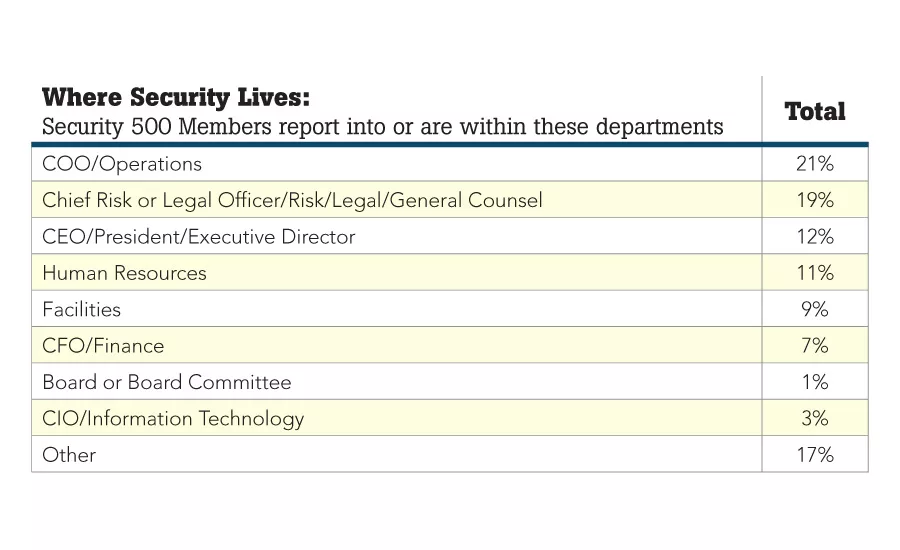
But even though only 35 percent of Security 500 members report direct responsibility for cybersecurity, CISOs and CSOs who can convey the importance of cybersecurity to the board help to guide the organization’s navigation forward in today’s cyber-driven world.
According to Cyber Tactics columnist Steve Chabinsky, in his reporting of the Cybersecurity Myths, (www.securitymagazine.com/articles/86326--CyberMyths) the number one myth is The IT Responsibility Myth: “Cybersecurity is primarily an Information Technology issue that can be automated.” Chabinsky comments that “The IT Responsibility Myth is particularly dangerous because it underestimates security requirements and lets Boards of Directors and C-Suite Executives off the hook. Information and network security must be addressed within the larger framework of enterprise risk management. Anything less fails to place cybersecurity into its greater business context and makes success more difficult.”
3. Terrorism
The number of terror attacks world-wide shot up by 35 percent between 2013 and 2014, with an 81-percent jump in the number of deaths, according to the State Department’s annual global terrorism report. The report said nearly 33,000 people were killed in almost 13,500 terrorist attacks around the world in 2014, up from just over 18,000 deaths in nearly 10,000 attacks in 2013. There were 20 attacks that killed more than 100 people each in 2014, compared with two in 2013, according to the report.
The report attributes the rise in attacks to increased terror activity in Iraq, Afghanistan and Nigeria and the sharp spike in deaths to a growth in exceptionally lethal attacks in those countries and elsewhere. There were 20 attacks that killed more than 100 people each in 2014, compared to just two in 2013, according to the figures from the State Department.
An anti-terrorism practice at United Airlines, according to Rich Davis, Managing Director of Global Security and Compliance, is building relationships with regulators such as the Transportation Security Administration (TSA), the Federal Aviation Administration (FAA), and other governments around the world.
The biggest security challenge in Davis’s sector is simply that airlines tend to be a major target. “That is what has driven the important relationships with the other airlines, with the regulators, and with the intelligence community of the U.S. government and other governments,” he says. “When there is a history of successful terrorist plots, you understand why that makes what we do so important to our companies.”
4. Business Continuity
As of the writing of this report, Hurricane Matthew had made landfall in Florida, after causing deaths and damage in the eastern Caribbean. Severe weather is a shared worry among consumers and business leaders, according to the Top Travelers Risk Index. Thirty-nine percent of consumers and 33 percent of business leaders indicate that they believe damage to their property is more likely to occur. Sixty-three percent of consumers say they have a plan for what to do before extreme weather strikes. About half of business leaders say they have a business continuity plan in place. The number of weather-related deaths in the U.S. rose to almost 500 people in 2015, according to the NWS Office of Climate, Water and Weather Services and the National Climatic Data Center.
Security 500 enterprise security leaders rank this as the number four concern, although you’d be hard pressed to find any that don’t have some type of business continuity plan that isn’t tested, modified and re-tested frequently. You are prepared! Increasingly, GSOCs are used and recognized as a necessity to support business goals and operations for business continiuty. Corning, Inc.’s GSOC, led by Steve Harrold, CPP, Division Vice President, Global Security, offers unprecedented enterprise situational awareness to identify threats and related vulnerabilities, in addition to enabling effective communication and mitigation against risk before a security-related event occurs, including weather. Many GSOCs now employ special personnel dedicated to watching the weather and communicating weather-related threats to the CSO.
5. Budget and Funding
Hampering the ability for security executives to mitigate security risks is the challenge of secure sufficient funding to do so. According to a survey from The Institute of Information Security Professionals (IISP), security budgets are increasing, however, not as quickly as they should in order to mitigate risks.
However, this year’s survey results show that 64 percent of Security 500 members increased their budgets in 2015, with 23 percent reporting that the budgets stayed the same and 13 percent reporting a budget decrease. In 2014, 65 percent of Security 500 members reported their budgets increased over the prior year.
The reasons vary, but overall, budget increases are getting support because organizations and C-suites understand and embrace security’s role and success in mitigating risks, which are illustrated via metrics and measures.
Budgets are getting C-suite support because Security 500 participants are becoming the bridge connecting the two worlds of business and security and to be “customer facing.” More and more, security is participating in completing proposals, giving prospects tours of their security departments and engaging with customers.
Another good practice is to be creative, as Harold Grimsley, CPP, director, corporate safety, security and building services for Blue Cross Blue Shield of Florida, recently did. Grimsley had an off-site parking lot that was experiencing some minor crime. It was controlled by two security officers. Not having any extra funding in place, Grimsley resurfaced the lot, improved the fencing, installed IP surveillance cameras and added an access control system with intercoms. The total project cost was $150,000, but the security officers were no longer needed and the project was amortized over a five-year period. The savings was $238,000. “We saved more money because it was a good business decision,” he says. “I improved my security and I saved the company money as well. It also gave us the ability to try out a new wireless technology.”
6. Asset Protection, Theft and Investigations
Security enterprise executives ranked asset protection and theft as number seven on the top 10 Trends. According to the 2016 ACFE Report to the Nations on Occupational Fraud and Abuse, the typical organization loses five percent of revenues in a given year as a result of fraud. The total loss exceeded $6.3 billion, with an average loss per case of $2.7 million. The median loss was $150,000, with 23.2 percent of cases causing losses of $1 million or more.
In retail alone, the 2016 National Retail Security Survey found that inventory shrink averaged 1.38 percent of retail sales, or $45.2 billion in 2015, up by $1.2 billion from 2014. According to the report, 47 percent of retailers surveyed reported increases in overall inventory shrink in 2015, with shoplifting accounting for the greatest cause with an average loss of $377 per incident (39 percent), up nearly $60 from 2014.
One practice comes from Gene W. James, CPP, Director of Asset Protection for Jack in the Box. James says that theft protection techniques, such as background techniques, are the absolute cornerstone of any program, but are only as good as the information provided by the applicant. It is essential that management reviews every employment application, he says. He also mentioned conducting pre-employment behavioral testing and the establishment of an interview protocol.
Ethics and security awareness/training are important as well, and training programs need to encompass new hires, he says. “You also need policies and procedures that lay out who investigates theft and how terminations are handled after you find a theft… Inspect what you expect,” he adds.
At Walmart, a restorative justice program from the Corrective Education Company (CEC) benefits both shoplifters and stores. If a participating retail store catches someone stealing merchandise, they give the shoplifter a choice – either the store calls the police, or the shoplifter can agree to sign up for a shoplifting education course that is administered by CEC. Read more about Walmart’s CEC partnership in this month’s Security Talk column on page 10.
7. Training and Employee Hiring and Retention
Security 500 leaders report responsibility for employee hiring, training and retention. There are many enterprise security programs popping up at universities around the country, including Miami Dade College (MDC), which will become the first educational institution in Florida to offer an undergraduate degree in data analytics.
Internally, training takes many forms, and good practices in this area come from George Frandsen, Senior Director of Safety and Security for Guidewell. “As a department, we provide employees with emergency response training that they can use at work or in their personal lives,” Frandsen says. “For example, two years ago, we teamed up with the University of Florida to offer hands-only CPR training to employees. We’ve now trained more than 600 employees in this technique.”
8. Technology and Contract Management and Maintenance
Walk through the tradeshow floor at ISC West or ASIS, and you’ll see hundreds of security products peddled by vendors wanting to sell you the “latest and greatest” in security technology. But sometimes, you don’t need technology as much as you need someone to sit down with you and have a frank and honest conversation about what you should or should not install in your enterprise. Then you can talk technology, right? Of course, it all depends upon your situation, your environment and the risks that you are trying to mitigate, but who wants to be sold something that they don’t need or can’t use?
That’s where many Security 500 members rely on their integrator partners, as about 90 percent of Security 500 members have responsibility for security technology and integration.
This area, in particular, is where a good practice may come into play even more, as a school district with 1,000 students doesn’t need the same technology as one with 10,000 students.
Eric O. Martin, PSP, Manager, Global Security Systems & Compliance for Halliburton in Houston, has in-house personnel that handle the configuration and the front-end work security work in 120 countries where Halliburton has a presence, so his integrator needs are smaller. “I design our security systems down to the smallest details, so a small company could take the package and understand the consistency that I want.”
A trusted partnership with an integrator is the goal for William N. Wilkins, who is Director, Global Technical Projects for Valero Energy Corporation. “I am not the integrator’s customer; we have the same customers,” he says. “The success of our security program is equally dependent on the performance of both groups, and as such we are on the same team.”
When resources permit, Wilkins says, companies should strive to develop their own specifications and scope for security technologies. “I have always equated this to the purchase of a vehicle,” he says. “You wouldn’t allow a car salesman to pick out your next car, so why would you allow an integrator to pick out your next enterprise platform? We use our integrator to vet our specifications and recommend product lines they have had success deploying. We marry this with an internal product evaluation process to ensure we have the best product for our application. We then provide design for the overall project scope – to include all infrastructure requirements.”
9. Executive and Employee Travel
Companies have a “Duty of Care” and “Duty to Warn” responsibility when it comes to employee travel and foreign assignments. According to the annual Vacation Confidence Index from Allianz Global Assistance, 86 percent of Americans are concerned about terrorist attacks occurring while on vacation in various regions of the world, prompting many to make major changes to their travel plans. Americans are most concerned about attacks in the Middle East, Europe and Africa.
While American consumers can change their travel plans, often business employee and executive travel is necessary to continue global growth.
On March 5, 2013, Venezuelan president Hugo Chavez died, triggering political unrest and protests across the country. Airports were closed, roadways blocked and gunshots were heard in the country’s capital. Mourning, unruly crowds took to the streets as businesses shuttered their doors, bracing for riots and violence. A group of protesters gathered around the Nielsen office in Caracas, shouting anti-American slogans.
Global companies like Nielsen, which operates in 106 countries, often face situations like that. A global economy offers unprecedented opportunity through new markets but with this also comes heightened risks for foreign employees. Managing these risks and preparing for volatile situations is a reality for global organizations today. In the Venezuelan case, swift action was put into place. “Within 45 minutes, we had armed security on the ground, getting the two Nielsen auditors and their families to a safe hotel because the airport was closed,” says Robert Messemer, Chief Security Officer at Nielsen. “We couldn’t put them on a plane that night, but we did the very next morning, and we got them safely evacuated.”
As Director of Global Security for Weatherford International Andrew Baer says that one of the obviously unique challenges of being in the oil and gas industry is the intrinsic risk in many of the operation locations, like the Middle East and Africa. “This is where the dual hat role comes about because my job is to protect people, but will all come together in a crisis management to respond when we have people in trouble,” says Baer. Between the political environment in which oil is extracted, the heavy machinery, the potential weather hazards, and the dangerous materials, “it’s a very complex and risky environment in which to operate on a day by day basis,” Baer says. “The nature of our industry is to go to the places where we can extract oil, and those places are not in the easiest parts of the world to operate.”
For Donald Hill, VP and Head of Global Security and Safety, expanding Visa to different parts of the world is one of the unique security challenges Hill finds specific to his job. “It’s just our world environment right now,” he says. “Literally within the past year, we talk about all the terrorist attacks, and we’ve had staff or offices in those locations. We’re not far from the actual center of impact. Those are the things that keep you up at night. In each of those cases, we were on the phones reaching out, trying to make sure we could account for everyone.”
10. GSOC Management
For the first time, Security 500 members included Global Security Operations Center (GSOC) Management on the top 10 trends.
A GSOC can take the form of new facility or can be housed in an existing one. And one size does not fit all with a GSOC, of course. Factors such as enterprise size, security budget and risk needs analysis all come into play. Even more, a GSOC’s value is now recognized as a necessity to support an enterprise’s global business goals and operations.
eBay, which has 35,000 employees and contractors in 40 countries, has 15 GSOCs that are named Central Security Control. The GSOC in San Jose, California, which is eBay’s corporate headquarters, is more strategic in nature. Regular meetings with the eBay security operations team and the GSOC team help to identify what’s currently on “the radar” in terms of security and risk management issues.
Exelon’s Security Operations Center (ESOC) has three entities: the ESOC, the Incident Command Center (ICC) and the Cyber Security Operations Center (CSOC). Together, the SOCs are a united physical and cybersecurity management organization tasked with mitigating and responding to physical and cybersecurity incidents. The group also is responsible for assisting other Exelon groups to ensure compliance with regulations such as NERC CIP, Sarbanes-Oxley, the Chemical Facilities Anti-Terrorism Standards, Pipeline Security and the Maritime Transportation Safety Act.
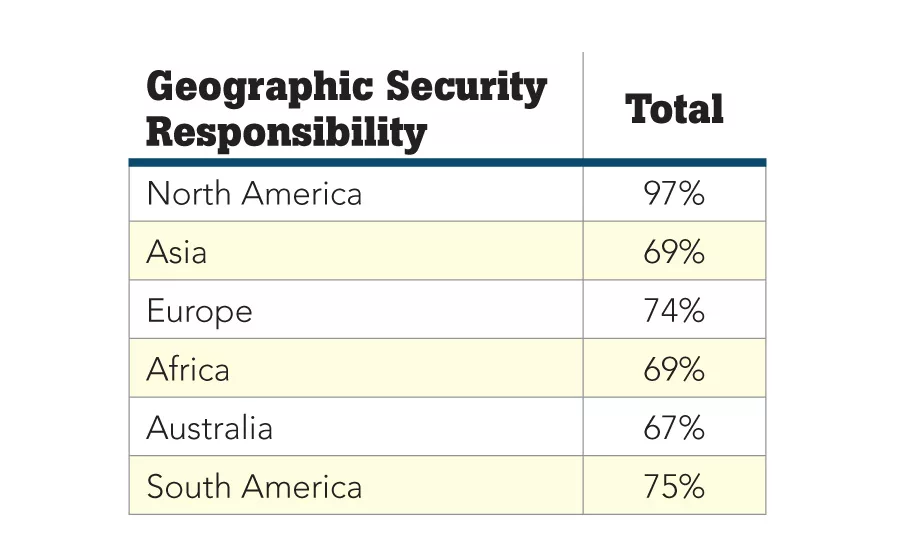
Microsoft Corporation has three GSOCs – one at the corporate headquarters in Redmond, Washington, that covers North America and South America, one in London (Reading) that covers Europe, the Middle East and Africa and a third in India that handles the Asia Pacific region. “Everything is tied into the GSOCs,” explains Mike Howard, CSO at Microsoft. “We built the technology so that if one goes down, another one could easily assume all of the load sharing and can access cameras, lock down doors, dispatch security officers and more. Each GSOC is staffed with between eight and 10 operators who are indigenous to the area. They are there to manage the intake for calls into our system, including security issues and alerts. After that, we leverage our Regional Security Managers and others within Global Security. If it’s a crisis management issue, regional mangers drive the crisis management process. A lot of it is process driven with protocols.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!