Lookin’ Good
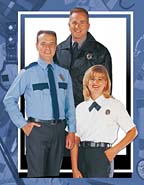
In the United States, there are hundreds of thousands of security officers – some say 900,000 to 1.2 million people employed. Some years ago, dress was typically police or military look. Today the look varies depending on the assignment, location, corporate culture and depending on the contracted security firm.
A couple of years ago, Jim Costello, CPO, CPP, CHPA, writing in the Protection Officer News, reported on a survey of healthcare officers. The Protection Officer News is a publication of the International Foundation for Protection Officers, Naples, Fla.
Costello found that most officers wore police or military style uniforms, some wore blazers and slacks with a security patch indicating the healthcare facility while fewer wore casual clothes. Security magazine surveys over the years reinforce Costello’s findings. In fact, since September 11, there has been an increase in police and military style uniforms.
At the same time, there has been growth in casual dress as more security officers interact with the public.
Firms such as Lion Apparel of Dayton, Ohio, which provides uniforms to thousands of contract officer firms, track trends but also see some consistency – a desire to identify the contract firm or the site customer in some way within the uniform.
According to the Costello survey, the police and military look is appropriate because it is a crime deterrent, it more easily identifies the responder during an emergency and because the officers like the look.
On the blazer side, most say the look is there because of the need for the officers to provide public relations and customer relations tasks or because the hiring organization wanted a lower-key security operation.
It’s obvious that there will be continued growth of the number of security officers and the number of those officers dressed in police and military uniforms. In recent Congressional testimony, Robert Liscouski, assistant secretary for infrastructure protection, U.S. Department of Homeland Security, confirms that terrorists are willing to exploit a wide range of infrastructure vulnerabilities. “That is why we must continue to be vigilant and flexible in our approach to infrastructure protection.” Liscouski’s Protective Security Division (PSD) works with owners and operators of specific categories of critical assets to develop and tailor protective practices for these assets. An example of this type of product is the guidelines for protecting refineries that the oil industry published last year. In addition, PSD is deploying regional/ field security representatives to work directly with the owners and operators of critical infrastructure facilities and community leaders to address protective measures.
There is no doubt that, as more security officers are hired, most will wear uniforms with a police or military look.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




