Plant Security: Who Needs a PC?
Count Me In LLC of Mount Prospect, Ill., a biometrics manufacturer, wanted to offer its customers an easy, affordable way to implement USB finger-scan devices and relays for access control. The company’s primary obstacle was eliminating the expense of installing a PC biometrics terminal at each doorway. They also wanted to utilize the Ethernet infrastructure already in place at customer sites.
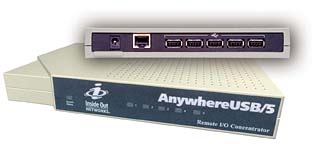
USB hub approach
The company tested AnywhereUSB/5 from Digi of Minneapolis. The Ethernet-enabled USB hub employs USB-over-IP technology, allowing such devices to be connected anywhere on a network without a locally attached host PC. Instead of having a PC or expensive terminal at each point of entry, the manufacturer could offer the hub for roughly half the cost of a traditional biometrics terminal.“Digi enabled a more cost effective and flexible solution,” said Neal Katz, vice president of Count Me In LLC. “We extended our technology’s use by implementing the AnywhereUSB in conjunction with our Door Monitor access control system. This allows us to take advantage of a building’s existing wiring and go into areas where PCs are not conducive. Our Door Monitor is now of value in increased applications, and the cost to our customers is reduced.”
Implementing the technology involves three basic steps. First, the company connects the hub and accompanying finger-scan device at each doorway to an Ethernet via RJ-45 cable. Next, the access control application software is installed on a single host in the main security office. Third, USB-over-IP software drivers are loaded onto the same host.
This software acts as a COM port redirector; it makes the host think that the remote AnywhereUSB devices are locally attached. All processing happens at the remote host, resulting in fewer points of failure and less risk of tampering. Connecting the biometrics device to the AnywhereUSB provides a cost-effective alternative to traditional host-based access control systems.
Count Me In’s Door Monitor access control system is used to monitor and control people who are allowed to enter a building or room. It combines the company’s biometrics fingerprint with easy-to-customize software.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






