Why Security Needs a ‘Great Conversation’
|
In my role as a strategic advisor, I am asked by executives to help them plan, execute and measure their business model and strategy. The desired outcome is achieving a strategic value position in their market. As well, we help them deliver on that promise, through an empowered leadership culture and performance-based operations model.
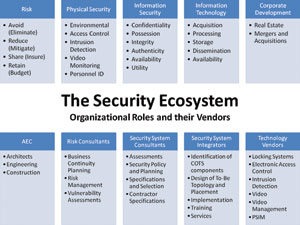
But what if ‘Security’ was my client? What if I had to answer to the entire Security Ecosystem that connects such constituents including:
• The Security Executives and their team, which includes:
1. The Chief Executive Officer and Executive Team, as well as the Board of Directors.
2. The market ecosystem they live in and their supply chain that helps them deliver on the promise, including their employees.
• The Security vendor community that supports the strategy, planning, execution and measurements that undergird the security industry.
How would Sage help ‘Security’, as a client, create a strategic value position within all global markets and channel verticals?
We would begin with establishing the baseline measurement of performance. This would be defined by Sage as the Mind of the Companysm, Mind of the Marketsm and Mind of the Investorsm. For an organization, we are looking at how it measures itself from a market, operations, and investor perspective. Then we look at how their market and investor ecosystem is performing and measuring itself. The difference is the potential value gap or the opportunity to target a seam in the market that is not being addressed.
When we change our perspective to looking at security, as if it were an organization, we discovered in 2002 a startling disconnect between each constituent in the ecosystem.
Using the analogy of an organization, it became apparent there were standalone silos operating independently within a narrow definition of value. Based on Sage’s experience, when we see this happening, we can predict several things:
1. The organization’s business model is incurring needless cost.
2. The organization’s ability to engage the market is sub-optimized.
What is negative can be turned into opportunity by restating the above:
1. If we can find money and resources within our current cost model .
2. Then we have the opportunity to fund innovation, adding value to the organization.
The result of both of these is: “We have the opportunity to be more valuable to ourselves, to our customers and constituents as well as to our market.”
In Sage’s interviews with a representative sampling of the Security Ecosystem there are some conclusions drawn regarding the security ecosystem with the full knowledge that there are exceptions, some quite extraordinary, among us.
The Security Executives and Their Team
Answering the questions:
• Who is the ‘Security Executive’?
• What is their perceived function and value?
• What composes their ‘team’?
• What does this ‘team’ do?
We found that the Security Executive was rarely part of the Executive Management Team (EMT) reporting to the CEO. They most often could be found under the CEO’s direct report in Operations or Finance reporting under a Facility Group head. Of course it varied by size of company and vertical market, but the organization’s perception from executives to employees, placed them in a facility-type role. Very rarely do we see them working in conjunction with the Information Security Officer although their software, equipment, people and processes could be optimized and leveraged by that relationship.
The Security Market has a name that matches this designation well: ‘Physical Security’. The implication is that the focus is on the security of tangible assets or things. So security executives must ensure the organization’s tangible assets are physically secure.
It is no wonder most physical security executives come from law enforcement. We want experienced professionals that know how to keep bad guys from getting to our things or hurting our people.
Security Client and the Ecosystem
But, ultimately, the Security Executive has a client; the CEO. And that client is responsible for the vision, mission and value of the organization. The CEO is supported by the Board of Directors. The successful CEO has a ‘business model.’ As well, they are responsible for defining and advancing the organization’s strategic direction while delivering on the performance metrics communicated to the Board. Those metrics should include not only direct performance goals like revenue and profit, but value drivers that grow the company and protect its position of value in the market. This could include market and operational efficiency drivers.
The CEO and Board must also be cognizant of risks, especially if they are subject to regulations and/or a public company or government organization.
If the CEO and Board have these metrics, and they are the right metrics, how effective do you think they are in driving behavior and performance against these goals all the way through the organization?
We did a poll to test this and found that it rarely was communicated to the Security Organization, and, if it was, it rarely became connected to the Security Organizations behavior: that is, their strategy, management and measurement.
Security’s Vendors
We also found a gap in the vendor ecosystem. In our interviews with technology vendor’s (software and hardware), integrators and consultants, we attempted to understand understand their knowledge of their clients (security management’s) performance model and whether it was linked to how they, the vendor, were being measured. It was not. In fact, we rarely found any knowledge or behavior that was. The vendor community is rarely seen as anything more than a transaction-based delivery mechanism for a ‘construction project’; either retrofit or new construction.
It turns out, in most cases, the business drivers that should influence and drive security’s mission were not even a topic of conversation…That is a lost opportunity for everyone.
The Great Conversation™
Every one of the security constituents gravitates to being laser focused on their silo. As a result it is negatively impacting the potential value that could be delivered and represents a missed opportunity. It is incurring cost; money and resources that could be targeted to innovation but, instead, are used to manage an inefficient process model. There are few industry forums that address and discuss the ramification of how expensive, from both a cost and lost opportunity basis, this can be. Nor is there an industry methodology to assist the ecosystem in pursuing a higher order of value.
The good news: there is a growing realization to the opportunity and there are some early steps being taken. The Security Executive Council (SEC), a security executive membership community; PSA, an integrator membership community and certain forums like The Great Conversation that SEC and PSA are supporting, are attempting to bring this ecosystem together in new and compelling ways.
For industry participants each member of the security ecosystem has a compelling opportunity to resist silo agendas and chart their own collaborative ‘path to value’ contributing and making a higher value difference to their company, their own ecosystem and the industry as a whole.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





