Risk Analysis Methodologies
Before September 11, 2001, President Clinton signed Presidential Directive 63, the Policy on Critical In-
frastructure Protection. It identified eight (now 11) sectors of the economy considered critical to national security. Included are telecommunications, transportation, water supply, oil and gas production, banking and finance, electrical generation, emergency services and essential government functions. This directive, along with the Bio-terrorism Act and other implementing policies, assigned oversight of each function to a separate governmental agency. The protection of the water supply is the responsibility of the Environmental Protection Agency (EPA) and the protection of the food supply is the responsibility of the Food and Drug Administration (FDA). These agencies are assigned the task of developing risk assessment and security protocols for the protection of the assets under their purview, with many using a different risk assessment methodology.
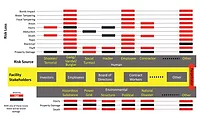
Many risk and vulnerability analysis methods exist. Although similar in nature, security professionals should be aware of the basics of these differing methodologies even if they are not involved directly in the function they assess.
Operational Risk Management
The FDA is responsible for the security of food production, importation, warehousing, transportation and distribution in the United States. This agency has adopted the Operational Risk Management (ORM) method to help ensure that food assets remain safe from attack.
ORM is an engineering-based risk management system used by the Federal Aviation Administration and the military to examine the safety and risk to existing systems. It is a tool designed to help identify operational risks and benefits to determine the best course of action for any given situation. It is defined as the risk of loss resulting from inadequate or failed processes, people and systems, or from external events. It is similar to other risk management methods in that it identifies hazards and determines the impact of food safety through estimating the probability and severity of an attack, allowing those responsible to focus on the worst hazard first. The FDA defines it as a defensive vulnerability assessment tool to identify points in a system that are most susceptible to terrorist attack and to design preventative measures to reduce risks. It uses a six-step process that includes identifying the hazards, assessing the risk, analying risk control measures, making control decisions, implementing risk controls, and supervising and reviewing.
Identify the Hazards–The first step examines each activity in a process or flow of actions and events and identifies the associated hazards. ORM defines a hazard as any real or potential condition that can cause degradation, injury, illness, loss of equipment, or property damage. In the case of restaurant food security, a process may include the placement of food in a salad bar. The associated hazards include intentional contamination with bacteria, the placement of sharp objects inside the food, or the introduction of a poison.
Assess the Risk–Hazard probability, severity, and exposure (the number of people or resources affected by a given event or cumulative events) are determined in terms of their impact on people and food security. ORM uses the probability categories of frequently, likely, occasional, seldom and unlikely. In the context of food security, each probability term has a definition. Frequently takes place often, and persons are continuously exposed. Likely takes place several times, and persons are regularly exposed. Occasional will happen, and exposure is sporadic. Seldom may happen, and exposure is infrequent. Unlikely likelihood and exposure are rare. Severity is categorized as catastrophic, critical, moderate or negligible. Catastrophic is a complete business failure or loss of facility asset due to attack resulting in fatalities. Critical is major business impact resulting from severe illnesses or incident. Moderate is minor business impact resulting from minor illnesses or incident. Negligible is less than minor business impact or illness. Risks are then ranked using a matrix.
Analyze Risk Control Measures–This step represents the development of risk control measures to mitigate, prevent, control, or eliminate the hazard or reduce its probability or exposure.
Make Control Decisions–In the ORM methodology, decision makers who can implement the control measures are identified. ORM does not assume this is a singular person or department.
Implement Risk Controls–Once the controls and those responsible for the implementation of the controls are identified, the process of executing protective measures begins. Implementation strategies are developed that define individual responsibility, accountability, and involvement. ORM allows for different people to implement the controls based on severity.
Supervise and Review–Once controls are in place, their effectiveness is examined and reevaluated. Additional assessment is completed as the system changes. The following principles apply to all stages of the ORM process: Accept no unnecessary risk. Unnecessary risk comes without a commensurate return in terms of benefits or opportunities.
Make risk decisions at the appropriate level. Making risk decisions at the appropriate level establishes clear accountability. The decision maker is the person who can allocate the resources necessary to implement controls or is authorized to accept risk.
Accept risk when the benefits outweigh the costs. All identified benefits should be compared with all identified costs. Balancing costs and benefits can be a subjective process.
Integrate ORM into planning at all levels. The later changes are made in a process of planning and executing an operation, the more expensive and time-consuming they can become.
Angel Flight South Central helps patients who do not have access to conventional transport or who are too ill to be driven or fly on a commercial service. Private pilots volunteer their planes and time to take people from their local airstrip to hospitals and clinics in other cities, often combining in relays so that a journey of thousands of miles can be made.
Working through its partner ADI, security video vendor Rainbow donated six vandal-proof hammer tough dome camera units for use at Houston Hobby’s hangars and a new 1,500 sq ft facility where patients wait in privacy for transportation and their pilots study routes in a planning room.
The housing has a half-tint polycarbonate dome, is IP66 rated and can handle heavy impact. In all but extreme contacts only the dome is scratched while the camera remains intact.
Angel Flight South Central flew 3,000 missions in 2005, operating from Texas, Arkansas, Louisiana, Oklahoma and parts of New Mexico, Mississippi and Western Tennessee. The charity also organizes general humanitarian flights and was active in the aftermath of Hurricane Katrina when its pilots demonstrated exceptional dedication.
Many of the passengers who take the South Central flights receive treatment at a cancer center within the University of Texas or the Texas Children’s Hospital in Houston. On arrival at their destination airport, patients are met by a ‘ground angel’ and driven to the medical facility.
The USDA defines CARVER + Shock as an offensive target prioritization tool to identify critical nodes most likely to be targets of terrorist attacks and to design preventative measures to reduce risk. It is used in conjunction with ORM. CARVER + Shock considers seven factors that affect the attractiveness of a target:
Criticality: the degree to which the public health and economic impacts achieve the attacker’s intent. How important is the target as determined by the impact of its destruction on operations?
Many risk and vulnerability analysis methods exist. Although similar in nature, security professionals should be aware of the basics of these differing methodologies even if they are not involved directly in the function they assess.
Operational Risk Management
The FDA is responsible for the security of food production, importation, warehousing, transportation and distribution in the United States. This agency has adopted the Operational Risk Management (ORM) method to help ensure that food assets remain safe from attack.
ORM is an engineering-based risk management system used by the Federal Aviation Administration and the military to examine the safety and risk to existing systems. It is a tool designed to help identify operational risks and benefits to determine the best course of action for any given situation. It is defined as the risk of loss resulting from inadequate or failed processes, people and systems, or from external events. It is similar to other risk management methods in that it identifies hazards and determines the impact of food safety through estimating the probability and severity of an attack, allowing those responsible to focus on the worst hazard first. The FDA defines it as a defensive vulnerability assessment tool to identify points in a system that are most susceptible to terrorist attack and to design preventative measures to reduce risks. It uses a six-step process that includes identifying the hazards, assessing the risk, analying risk control measures, making control decisions, implementing risk controls, and supervising and reviewing.
Identify the Hazards–The first step examines each activity in a process or flow of actions and events and identifies the associated hazards. ORM defines a hazard as any real or potential condition that can cause degradation, injury, illness, loss of equipment, or property damage. In the case of restaurant food security, a process may include the placement of food in a salad bar. The associated hazards include intentional contamination with bacteria, the placement of sharp objects inside the food, or the introduction of a poison.
Assess the Risk–Hazard probability, severity, and exposure (the number of people or resources affected by a given event or cumulative events) are determined in terms of their impact on people and food security. ORM uses the probability categories of frequently, likely, occasional, seldom and unlikely. In the context of food security, each probability term has a definition. Frequently takes place often, and persons are continuously exposed. Likely takes place several times, and persons are regularly exposed. Occasional will happen, and exposure is sporadic. Seldom may happen, and exposure is infrequent. Unlikely likelihood and exposure are rare. Severity is categorized as catastrophic, critical, moderate or negligible. Catastrophic is a complete business failure or loss of facility asset due to attack resulting in fatalities. Critical is major business impact resulting from severe illnesses or incident. Moderate is minor business impact resulting from minor illnesses or incident. Negligible is less than minor business impact or illness. Risks are then ranked using a matrix.
Analyze Risk Control Measures–This step represents the development of risk control measures to mitigate, prevent, control, or eliminate the hazard or reduce its probability or exposure.
Make Control Decisions–In the ORM methodology, decision makers who can implement the control measures are identified. ORM does not assume this is a singular person or department.
Implement Risk Controls–Once the controls and those responsible for the implementation of the controls are identified, the process of executing protective measures begins. Implementation strategies are developed that define individual responsibility, accountability, and involvement. ORM allows for different people to implement the controls based on severity.
Supervise and Review–Once controls are in place, their effectiveness is examined and reevaluated. Additional assessment is completed as the system changes. The following principles apply to all stages of the ORM process: Accept no unnecessary risk. Unnecessary risk comes without a commensurate return in terms of benefits or opportunities.
Make risk decisions at the appropriate level. Making risk decisions at the appropriate level establishes clear accountability. The decision maker is the person who can allocate the resources necessary to implement controls or is authorized to accept risk.
Accept risk when the benefits outweigh the costs. All identified benefits should be compared with all identified costs. Balancing costs and benefits can be a subjective process.
Integrate ORM into planning at all levels. The later changes are made in a process of planning and executing an operation, the more expensive and time-consuming they can become.
SIDEBAR: Risk Solution – Angel Flights Use Dome Cameras
A charity that flies needy and vulnerable people for medical purposes is using dome cameras at a facility within Houston Hobby Airport.Angel Flight South Central helps patients who do not have access to conventional transport or who are too ill to be driven or fly on a commercial service. Private pilots volunteer their planes and time to take people from their local airstrip to hospitals and clinics in other cities, often combining in relays so that a journey of thousands of miles can be made.
Working through its partner ADI, security video vendor Rainbow donated six vandal-proof hammer tough dome camera units for use at Houston Hobby’s hangars and a new 1,500 sq ft facility where patients wait in privacy for transportation and their pilots study routes in a planning room.
VANDAL-RESISTANCE
The high-resolution color dome is designed for any application such as an airport, school or civic area where there is a need to protect the camera from accidental or deliberate blows. Integrators recognize the benefits of the dome’s 3-D gimble bracket, which allows the user to pan, tilt and rotate the camera towards the side, so making wall mounting more effective.The housing has a half-tint polycarbonate dome, is IP66 rated and can handle heavy impact. In all but extreme contacts only the dome is scratched while the camera remains intact.
Angel Flight South Central flew 3,000 missions in 2005, operating from Texas, Arkansas, Louisiana, Oklahoma and parts of New Mexico, Mississippi and Western Tennessee. The charity also organizes general humanitarian flights and was active in the aftermath of Hurricane Katrina when its pilots demonstrated exceptional dedication.
Many of the passengers who take the South Central flights receive treatment at a cancer center within the University of Texas or the Texas Children’s Hospital in Houston. On arrival at their destination airport, patients are met by a ‘ground angel’ and driven to the medical facility.
SIDEBAR: CARVER + Shock
The U.S. Department of Agriculture (USDA) Food Safety and Inspection Service, in conjunction with the Homeland Security Office of Food Security and Emergency Preparedness, has adapted the U.S. Department of Defense’s military targeting method called CARVER + Shock to reduce or eliminate the potential risk at vulnerable points along the “farm-to-table” continuum. CARVER identifies vulnerabilities from a terrorist’s point of view.The USDA defines CARVER + Shock as an offensive target prioritization tool to identify critical nodes most likely to be targets of terrorist attacks and to design preventative measures to reduce risk. It is used in conjunction with ORM. CARVER + Shock considers seven factors that affect the attractiveness of a target:
Criticality: the degree to which the public health and economic impacts achieve the attacker’s intent. How important is the target as determined by the impact of its destruction on operations?
- Accessibility: physical access to the target. How easily can a target be reached, either by infiltration or with weapons?
- Recuperability: ability of the system to recover from an attack. How long will it take to replace or repair the target once it is damaged or destroyed?
- Vulnerability: ease of accomplishing an attack
- Effect: amount of direct loss from an attack
- Recognizability: ease of identifying a target
- Shock: psychological effects of an attack
About the Author
James F. Broder, CPP, CFE from Confidential Business Consultants LLC, has served as a special agent with the FBI, as a police advisor, overseas with the U.S. State Department, and as Special Assistant to the Chairman, Investigation Subcommittee, U.S. House of Representatives. Broder’s 2nd Edition of the Risk Analysis and the Security Survey is used extensively for Security Management Courses in universities and colleges all over the world. The book (Elsevier, Butterworth Heinemann), is available at $59.95 and can be ordered through the Elsevier Web site at www.elsevier.com or telephone (800) 545-2522 or write Elsevier, Order Fulfillment, 11830 Westline Industrial Drive, St. Louis, MO 63146.Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!