Understanding People, Your Enterprise’s Top Asset and Risk
Singing Kumbayah won’t keep insider threats away.
|
People are always viewed as the most important asset in your enterprise. There has been a significant amount of press about the increasing levels of external risk an enterprise must face on a day-to-day basis. Most experts agree that the “Insider Threat” is still one of the biggest risks.
The new hire process is the first line of defense for any enterprise. Locating the right individuals with the requisite knowledge, skill and experience is vital to any entity. Just as important, however, is making sure that each individual is a fit with the culture of an organization. Effective screening still is the first line of defense for an entity in managing its Human Capital Risk.
Once an individual has passed screening and assimilated into the organization, the risks increase exponentially and may manifest themselves in a number of different ways.
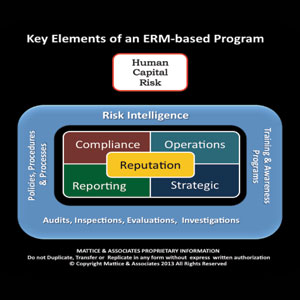
First among them is the obligation of providing a safe and secure work environment. Massive liability judgments have resulted from claims of sexual harassment, discrimination, negligent supervision and negligent security, just to name a few. Establishing solid policies, procedures and processes is vital. Deploying a risk-based triad of personnel, physical and information security policies and measures are important steps in creating and maintaining that safe and secure workplace. Part of providing a safe and secure work environment should also include employee assistance programs to help individuals in trouble. Emergency incident response programs are also important. Plus, there should be formalized workplace violence prevention and response programs in place with specialized training for supervisors and all employees.
Many enterprises today operate in far-flung places around the world. It is incumbent on the enterprise to provide guidance, assistance and proper safety and security support to individuals before and during these assignments. Assistance can cover a broad range of support that includes travel risk/security briefings, travel tracking, medical aid, close protection details and evacuation.
Many senior executives in global enterprises do not truly grasp the risks they face operating around the world. How many times have you heard senior executives say things like: “We are all one family here” or “One World – One Company?” While it may seem politically correct to try and establish a Kumbayahstyle environment, it also shows a high degree of naiveté and a lack of understanding of the dramatic cultural, societal and political differences that exist around the world. Enterprises that do not properly take into account and effectively manage these risks will face significant legal exposure that may take the form of civil liability and, in some cases, may result in criminal charges.
One illustration involves a typical entity’s ethics and governance program. Nearly every company doing business around the world has stated in their company’s values or guiding principles that they will comply with local laws. Now, take into account the highly publicized intellectual property mining by China. Few enterprises that either have a joint venture or key supplier in China understand that the value or guiding principal stated above provides a legal loophole authorizing the wholesale transfer of your intellectual property to the Chinese government. Article 18 of China’s State Security Law(paraphrased) states: Chinese citizens and organizations must faithfully furnish any information requested by State Security. Refusal shall be punished. It probably doesn’t much matter what you have stated in your employment agreement, teaming agreement or vendor/supplier contracts.
Executives need to check their Kumbayahmentality at the door or face a broad range of legal exposures. Many countries have very strong industrial policies and deploy their intelligence agencies to gain an economic advantage to support their economic growth. Understanding the full scope of risks in all the environments where you operate as well as the unintended consequences is vital to safeguarding the enterprise.
About the Authors:
Jerry J. Brennan is the founder and Chief Operating Officer of Security Management Resources (SMR Group), the world’s leading executive search firm exclusively focused in corporate security. Prior to founding SMR in 1997, Brennan enjoyed a 26-year career in domestic and international enterprise risk and security roles. Lynn Mattice is Managing Director of Mattice and Associates, a management consultancy focused at the development and alignment of Enterprise Risk Management and Business Intelligence Programs, as well as Intellectual Property Protection and Cybersecurity. He has more than 35 years of experience heading these programs at the executive level of three major multinational corporations and one mid-cap company in diverse industries.
Read moreLeadership & Management online at SecurityMagazine.com/Columns/Leadership
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






