ID SYSTEMS: Fingers Have the Touch

Logical access drives the appeal of fingerprint biometrics and will make it more appealing for physical access control, too.
To resolve today’s most common security issues – physical and logical computer access control – most enterprises use passwords, PINS, keys or tokens. However, even these most basic forms of access authorization have proven to be cumbersome and prone to theft or fraud. Individuals must remember an average of 30 passwords and PINS, and keys and tokens can be easily lost or stolen. Workers also can share their security passwords or devices to usurp security or time and attendance systems.
Biometrics has emerged as an important form of physical and computer network access control. And by far the most popular form of biometrics is fingerprint biometrics. For example, biometric fingerprint sensors from AuthenTec, Melbourne, Fla., are in nearly 6 million personal computers (PC), access control and wireless devices – more than any other form of biometric, according to Larry Ciaccia, the company’s executive vice president.
An ROI Change
In the past, cost, size and accuracy limited fingerprint use. Now, fingerprint sensors, once the size of a silver dollar and $50 each, are tiny slivers of silicon that cost under $5. Because of advances in technology, these sensors are accurate and practical for nearly any device. Today’s most advanced sensors use radio frequency (RF) to read below the surface of the skin, so more than just-washed fingers can open doors. These advances, combined with the growing world demand for security, have boosted fingerprint biometrics, which is doubling annually, and, according to industry analyst firm Frost & Sullivan, is estimated to top $1.4 billion by 2010.Commercial PCs and computer networks represent the fastest growing market for fingerprint sensors. These sensors are in more than 100 different PC, notebook, tablet and computer peripherals – by such mainstream manufacturers as HP, Fujitsu, Toshiba, Samsung, IBM and APC – restricting access to the device or designated programs and files, without the need for passwords. When linked with appropriate software, these fingerprint sensors can even restrict or track user changes to individual documents.
Some features and functions include:
- Advanced security to restrict access only to authorized users for individual or network computers.
- Password management, replacing the need for passwords on devices, programs, files and Web sites.
- Fast user switching to quickly and securely swap Windows desktop programs from one authorized user to another.
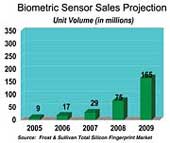
Biometrics in numerous forms will grow quickly, according to technology research firm Frost & Sullivan.
- A bank of unique biometric turnstiles to help protect a major financial institution in New York with more than 4,000 employees.
- A dual-mode smart card that restricts access at a secure government facility in Washington, D.C.
- Several major U.S. airports to restrict employee and contractor access in secure areas.
- A pharmaceutical factory to track employee productivity.
According to the Biometrics Industry Association, biometrics are technologies that automatically confirm the identity of people by comparing patterns of physical or behavioral characteristics in real time against enrolled computer records of those patterns. Leading biometric technologies accomplish this task by scanning patterns of the face, fingerprint, hand, iris, palm, signature, skin or voice.
Advantages
Biometrics is far superior to other common means of confirming identity, such as tokens (something one possesses) or passwords (something one knows). Tokens (drivers' licenses, for example) and passwords (Social Security numbers, for example) cannot ensure positive identification of a person. Tokens are routinely counterfeited and stolen. Passwords are routinely forgotten, left in plain sight, and stolen. Unlike tokens or passwords, biometric identifiers are inextricably linked to persons themselves and therefore cannot be forgotten, counterfeited or stolen.Biometrics help protect privacy by erecting a barrier between personal data and unauthorized access.
Technically, biometric capture devices create electronic digital templates that are encrypted and stored and then compared to encrypted templates derived from "live" images in order to confirm the identity of a person. The templates are generated from complex and proprietary algorithms and are then encrypted using strong cryptographic algorithms to secure and protect them from disclosure. Thus, standing alone, biometric templates cannot be reconstructed, decrypted, reverse-engineered, or otherwise manipulated to reveal a person's identity. In short, biometrics can be thought of as a very secure key: Unless a biometric gate is unlocked by using the right key, no one can gain access to a person's identity.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





