How Do Security Entrances Affect an Organization's Bottom Line?
Part 1: Defining Basic Tailgating Prevention Capabilities and Goals
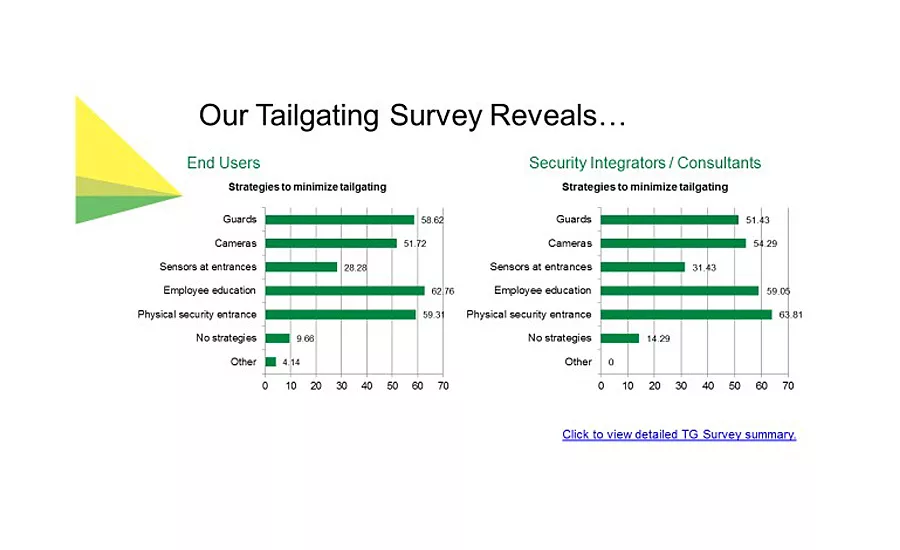
Above is an excerpt from a survey conducted in late 2014 by Boon Edam. It reveals that both end users and security professionals agree that there are three critically important components to a successful anti-tailgating strategy: Guard force, employee education, and technology mix. Read the full survey report here. Graphic courtesy of Boon Edam
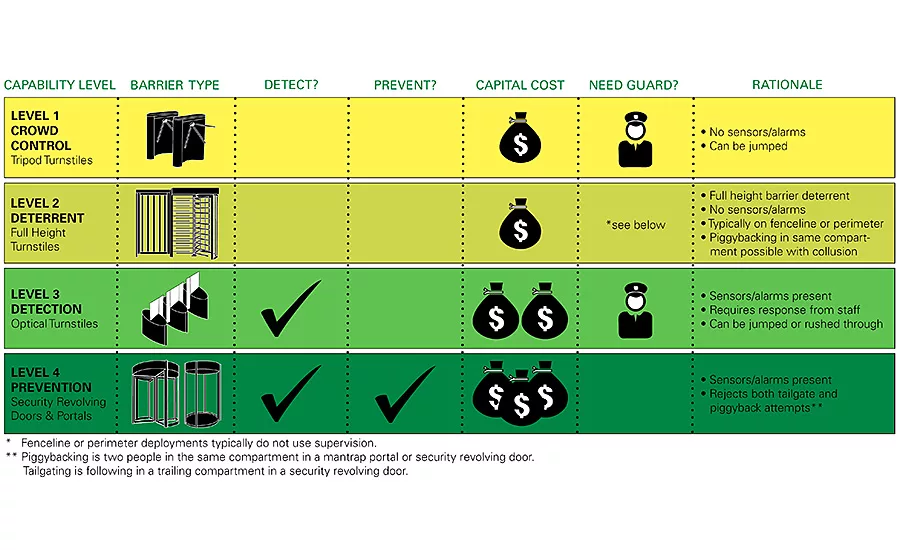
Table B: This graphic lists the four Capability Levels along with its associated security entrance type. A Capability Level can also be seen as a goal, e.g., “Do you want to detect tailgating or prevent it from happening?” Graphic courtesy of Boon Edam
Not all security entrances work the same way. Their different capabilities, therefore, have an impact on an organization’s overall anti-tailgating strategy in terms of capital outlay, manpower needed, annual operating costs, ROI, and user education and preparation.
In the image viewer above is an excerpt from a survey conducted in late 2014 by Boon Edam. It reveals that both end users and security professionals agree that there are three critically important components to a successful anti-tailgating strategy: Guard force, employee education, and technology mix. During his presentation at ASIS 2015, Chad Parris from Security Risk Management Consultants articulated a concise argument that “Technology does not equal Security.” Hence, an effective security strategy requires all three components to achieve results.
So, what is the best recipe for success within any given organization for the successful implementation of an anti-tailgating strategy? How does a given strategy affect an organization’s bottom line? These questions can be answered, but we first must understand the capabilities of security entrances themselves; capabilities which correspond to specific goals you want to achieve.
In Part I of this two-article series, we will introduce the four levels of anti-tailgating entrance capability based each product’s working principles. In Part II, we’ll delve into the impacts of each of the four Capability Levels to the organization in terms of recommended supporting security technologies, guard force, user education, financial costs, and the potential to measure results and gain a return on your investment. Table B above lists the four Capability Levels along with its associated security entrance type. A Capability Level can also be seen as a goal, e.g., “Do you want to detect tailgating or prevent it from happening?” Below, we’ll discuss further what is shown and hopefully dispel any myths or assumptions.
Level 1 – Crowd Control
“Crowd control,” related to tailgating prevention, means “High capacity controlled entry.” This Level is often deployed in areas where large numbers of people need to access a secure area during limited amounts of time, e.g., stadium entry, factory shift changes, transit terminals, or even an 8 a.m. rush into a high-occupancy, high rise building. This level employs simple technology to achieve the goal of high throughput, and offers the lowest capital cost. There are no detection sensors of any kind. But, it can be defeated by jumping over or crawling under the entrance. Therefore, manned security is needed to deter tailgating attempts and/or to respond quickly after an incident.
Level 2 – Deter
This Capability Level is a special one reserved for outdoor, perimeter locations on a fence line, such as entrances into parking areas or university campus dorm areas. The rugged, full height barrier serves as a deterrent to climb-over attempts. Full-height turnstiles and gates have a moderate capital cost and have no presence detection sensors or alarm systems. With collusion, two small people can physically piggyback in a single compartment. Due to being spread out over large distances, guards are typically not present to monitor such entrances continuously, thus this level is aptly named, “Deter.”
Level 3 – Detect
This level is where sensor technology comes into play to detect when tailgating occurs and to then sound an alarm. Optical turnstiles fall into this category, and they have a moderately expensive capital cost. It is important to know that tailgating is possible regardless of the height of the barriers; when the barriers open for a few seconds, a second person can rush through. This level, therefore, requires the presence of a guard to deter attempts and/or respond immediately.
Level 4 – Prevent
Level 4 is true tailgating and piggybacking prevention. The two entrances that can do this are a security revolving door and a mantrap portal. These entrances are the most expensive in terms of capital costs due to the sophisticated technologies within. However, no security guards are needed to monitor these entrances.
Note that multiple levels can be deployed on large campuses or even in the same building, but we’ll save that for another article. Now that we have reviewed the four Capability Levels, next we’ll discuss the impacts each of these levels has on an organization in terms of ongoing capital costs, user education, potential metric measurement and resulting ROI. Prior to reading Part II, I encourage you to pause and ask yourself, “What is at risk if the wrong person enters my building?” and, “How can I measure the success of my tailgating prevention strategy?”
Part II of this series is available here.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!









