‘Big Data’ a Soon-to-be Big Retail Deal
|
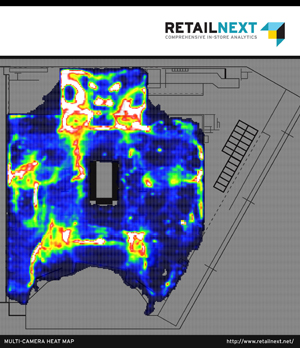
| New multi-camera heat maps make it possible for retailers to view shopper activity throughout the entire store in a single glance. Here, different colors represent degrees of activity, from white (most) to blue (least). Photo courtesy of PRNewsFoto/RetailNext Inc. |
“Big Data” was a hot topic for businesses and their IT operations last year. While Big Data is not going to be a mainstream concept for retail video surveillance this year, IMS Research (now part of IHS Inc.) predicts in its annual video surveillance trends that the use and aggregation of analytics and video feed metadata as Big Data will continue to grow, and that retailers as well as other businesses looking to utilize Big Data will increasingly look at the potential to incorporate video feed metadata streams into their data sets while leveraging the approach across security and the business as a whole.
Already, there are a few third-party firms serving retail establishments and who analyze security video feeds as well as other data – Big Data -- for typical and unique conclusions. In some leading edge cases, there now are more detailed detection and analytics of in-store traffic. Among examples:
Male vs. female demographics – New gender detection capability categorizes store visitors with very high accuracy, making this critical piece of demographic data available for analysis.
Employee detection – By assigning employees Wi-Fi-based identification tags to carry while working, retailers can obtain separate counts of shopper and employee traffic, enabling deeper understanding of what happens in stores.
New capabilities for presenting information make it easier for retailers to discover the insights they can use to improve the bottom line. Among examples:
Multi-camera heat maps – Combine views from contiguous cameras to create a single “kinetic” heat map for an entire sales floor, offering a true view of activity throughout the store.
Full mobile video support – The ability to view real-time or stored video from iOS and Android devices, offering access at anytime from anywhere.
Enhanced point-of-sale (POS) exception reporting – Increased capabilities to monitor store transactions for key indicators of fraud or theft, including “Top-N” queries for the most important metrics.
Legacy DVR integration – Enables retrieval and analysis of live and recorded video on popular DVR and NVR systems, unlocking legacy video from existing infrastructure without requiring additional capital expenditure.
Video interface and control enhancements – LP and other operations managers benefit from a cross-platform video player that works instantly on all Flash-compatible systems with no installation required, the ability to export multiple synched camera views in a single multi-pane video file and video interface enhancements for greater ease of use.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





