Home » Publications » Security Magazine
Security Magazine

2014 April
Cover Story
Back to TopHow can CSOs get the most out of their security systems integrator partnerships?
Read More
Featured Articles
Back to TopMitigating Retail Shrink with Better Monitoring
It doesn’t matter where you are in the world retail theft is a cost of doing business.
April 1, 2014
Using Architectural Elements for Stronger Security
When thinking of security, people tend to think of cameras, security officers and metal detectors.
April 1, 2014
How Remote Monitoring Adds Value from Afar
Remote monitoring services in intelligent buildings will continue to grow in usage during the next few years.
April 1, 2014
RSA Review: Converged Risk and the Internet of Things
The 2014 RSA Conference this February in San Francisco highlighted the theme of “Threat Intelligence.”
April 1, 2014
How Incident Reporting Can Mitigate Threats
What reporting strategies should your enterprise adopt?
April 1, 2014
How the Boston Marathon Bombing Changed the Game of Sports Security
One year ago, two bombs exploded at the Boston Marathon finish line, shocking the nation and driving international sporting event security changes
April 1, 2014
Reviewing Emerging Insurance Protection for Cyber Risks
Are you covered in the event of a cyber breach?
April 1, 2014
Banking Battlegrounds: Cyber and Physical Security Risks Today
What reporting strategies should your enterprise adopt?
April 1, 2014
Columns
Back to TopViews from a Top Integrator
Kratos PSS provides rapidly evolving technologies such as digital video analytics, LAN/WAN convergence and wireless solutions.
April 1, 2014
Testing Wireless Security Awareness at RSA
In February, a crowd of cybersecurity professionals attended the RSA Conference in San Francisco.
April 1, 2014
Top 5 Recommendations for International Active Shooter Risk Mitigation
Active shooter incidents continue to occur around the world as the most disturbing type of a workplace violence incident.
April 1, 2014
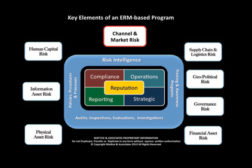
Measuring the Role of Risk Transfer in Cybersecurity Management
Recent events have catapulted cyber threats from a compartmentalized CISO responsibility to a boardroom discussion about director liability.
April 1, 2014
Elevating Cybersecurity to the C-Suite Before a Breach
Leading organizations are moving to the single office of the CSO and incorporating all aspects of security under a single leader, mission and plan.
April 1, 2014
Using NIST for Easier Cybersecurity Management
Corporate executives can develop enough expertise to comfortably navigate key cybersecurity risk management concepts
April 1, 2014
How to Keep Up with Emerging Technologies and Risks
consumers hundreds of billions of dollars annually. In the United States, credit card fraud resulting from cyber intrusions has skyrocketed.
April 1, 2014
Get our new eMagazine delivered to your inbox every month.
Stay in the know on the latest enterprise risk and security industry trends.
SUBSCRIBE TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing