Security Leadership and Management
Enterprise Services
The security industry can kick off 2026 the right way by investing in new talent.
Read More
SPECIAL REPORT
The Salary of a Chief Security Officer
The 24th annual Security and Compliance Compensation report gives industry professionals insight into what their peers are earning.
January 13, 2026
Integrated Solutions
Louder Than Words: How Effective Security Defends Brand Reputation
The roles of security and PR intersect when it comes to reputational protection.
December 19, 2025
Key Signs of Mental Health Struggles in Security
Listen to John Rodriguez, Founder of Empathic Security Cultures LLC, in this podcast episode.
December 17, 2025
Security Talk
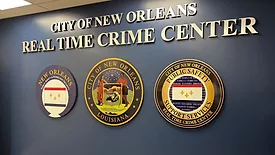
Inside New Orleans’ Real Time Crime Center
Director Ross Bourgeois explains how New Orleans built a 24/7 real time crime center that fuses video, CAD, LPR, and strict governance.
December 17, 2025
Leadership & Management
The Gift of Leadership
Security leaders discuss inspiring others through the gift of leadership this holiday season.
December 15, 2025
Career Intelligence
2025 Corporate Security Job Market Shifts
Adaptability is the foundation of resilience, both for corporate security programs and for individual security careers.
December 12, 2025
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing





.webp?height=168&t=1769044796&width=275)