Coronavirus Blogs
A centralized deployment reduces costs and is easier to use, giving public officials better tools for protecting their citizens.
Read More
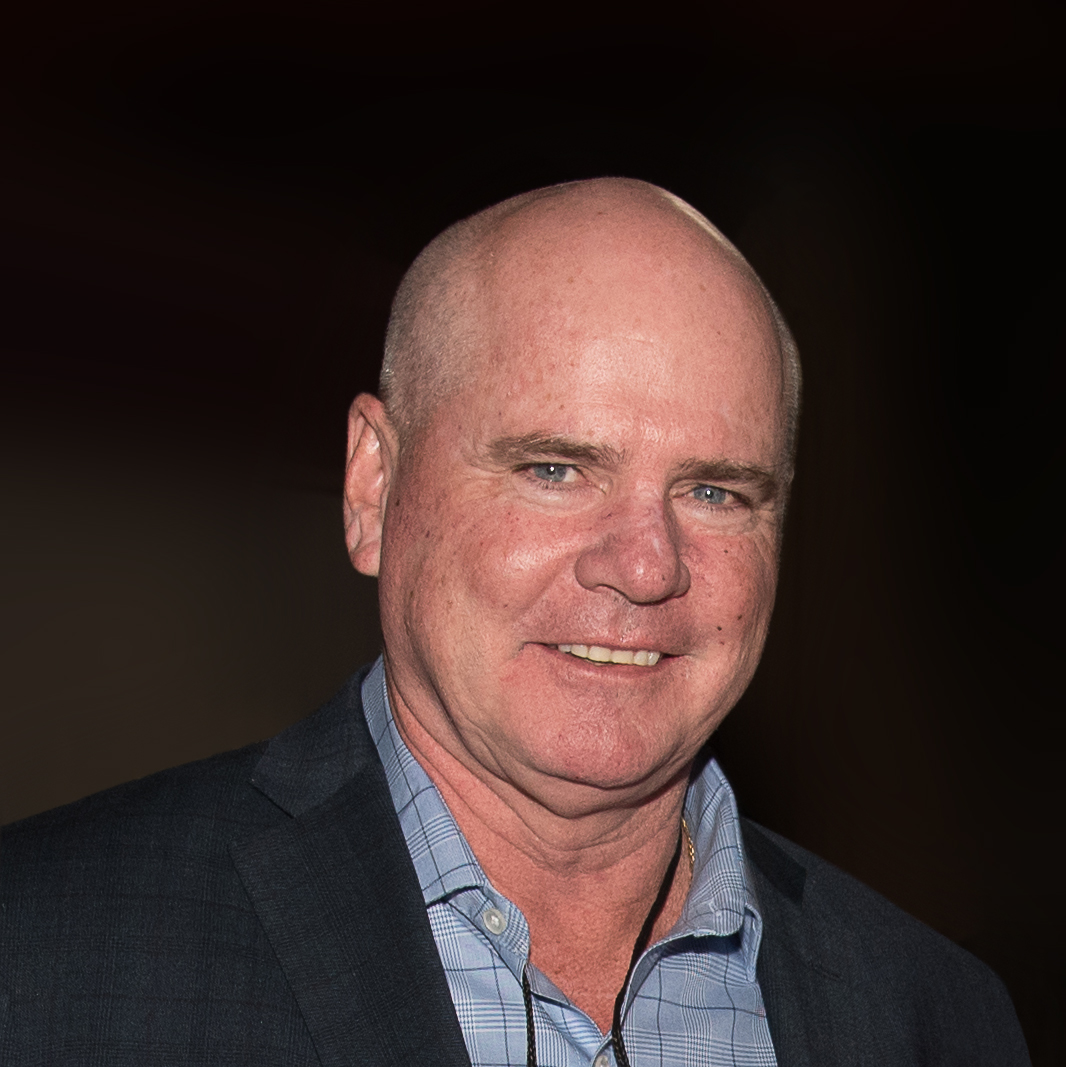
El Centro Regional Medical Center: Ensuring in-patient care during COVID-19
The Security Department at the El Centro Regional Medical Center maintained a compassionate, yet firm security presence, updating its pandemic response policies and processes, resulting in an orderly continuation of patient admissions and continuation of patient care.
May 12, 2021
ADM unlocks the power of existing data for COVID-19 response
ADM and its security team tapped into existing data, both inside the company and publicly available, to enable informed decision-making and real-time insight into the company’s pandemic response plan including contact tracing, location insight and information, and facility occupancy.
May 11, 2021
COVID-19 Heroes
Boeing values information as the backbone to pandemic response
Taking a project management approach to its comprehensive COVID-19 pandemic response, Boeing’s Security & Fire Protection and Health Services business units placed collaboration, communication and actionable data at the forefront to make unified, informed decisions across the enterprise.
May 7, 2021
Get our new eMagazine delivered to your inbox every month.
Stay in the know on the latest enterprise risk and security industry trends.
SUBSCRIBE TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing