
Back to Basics with Cloud Security
Organizations are doing some fancy footwork with security these days in order to simultaneously protect users yet empower them to perform various tasks online. As application workloads and activities move to one or more cloud environments, organizations have also begun to ask what they should do to ensure proper cloud security.
The answer, it turns out, has much to do with going back to basics as it does with anticipating what’s coming next in cloud-based security.
First Things First: What NOT to Do
When we advise clients to “go back to basics” for cloud security, we often look first at what they are doing now to secure their current IT environments. Such practices—whether good or bad—often extend to an organization’s use of hybrid and public cloud services as well.
For starters, we recommend abolishing some common, but risky security habits:
- Stop the use of manual, static or stale credentials. In the age of software-defined infrastructures and dynamic cloud services, it’s time to move from manual and often-unchanging user access methods. This includes:
- Stopping the use of static access keys that never expire.
- Stopping the use of access keys embedded in software code during application development or testing. These pose a risk if they remain in production code or in the event the code is subsequently uploaded to an open source repository, such as GitHub.
- Stopping the assignment of permissions that you forget to revoke when the need for access ends. Instead of assigning permissions that may last months or years, adopt a security posture that assigns permissions that last minutes or hours, especially for more sensitive and impactful data.
- Stop storing User IDs and passwords for longer than necessary. Given the growing focus on user privacy and regulations like the GDPR, it’s past time to start following some of the tenets adopted by the banking and payment card industry (PCI).
Just as those organizations don’t hold credit card information for longer than necessary, so too should today’s organizations keep user authentication data for only as long as needed, then discard it. Better yet, organizations should not try to take on the responsibility to hold user secrets they can’t protect properly. It may be time to pass on that responsibility to a third-party or cloud service expert in managing user identities.
Cloud service providers who deal heavily in user security and authentication are also increasingly moving toward a future that authenticates a user’s access via some type of trusted user account instead of via disparate, application-specific user IDs and passwords. This might include verifying user identities through a Microsoft Office 365 account, for instance, or through one of the user’s other social media networks or accounts. This means no longer creating a new User ID and password unique to your application or system. Instead, reuse trusted sources for identity and access management
- Stop giving administrators blanket access to everything, all the time. This practice may make an administrator’s life easier, but it has left a lot of damage and breached systems in its wake. Hackers often use such security loopholes with blanket Admin credentials to gain access to sensitive corporate data. Look into new solutions that easily control this type of access without causing a major headache for the administrators. Many do so while still ensuring appropriate governance.
Good Steps to Prepare for a Secure (Yet Cloudy) Future
We’ve covered many ways organizations tend to fall short in their security efforts. But, what can you start doing now to secure your emerging hybrid and multi-cloud worlds? To start, look to what leading cloud security providers have begun doing:
- Start replacing blanket permissions, user IDs and passwords with multifactor authentication (MFA) and privileged access management (PAM).
- Incorporate condition-based access to everything for everyone. The future will allow normal users to go about their day-to-day work without being constantly prompted for credentials. This will occur by monitoring behaviors and making appropriate decisions about when to escalate authentication and prompt for more layers of verification.
- Look to tools that use AI and machine learning to help evaluate log data and help flag the difference between typical user behavior and questionable behavior that might fall outside the norm.
- Start incorporating single sign-on for your users and customers, preferably from one cloud-based provider. For example, if you are using something like Active Directory in your on-premises environment, look for a provider that lets you automatically synchronize user login IDs/passwords from that system to a cloud counterpart. Similarly, consider offloading the hosting of user IDs and password databases to a reputable cloud provider.
- Consider federation to securely collaborate with business partners, third-party vendors and contractors vs. creating their own user accounts on your network.
If you are confused about what to do first, prioritize efforts based on low-hanging fruit. This means protecting and securing the highest risk users and data in your organization. This could be your executives, your HR team, your Finance team, your Legal team, or other IT administrators. Focusing in this way will reduce your risk exposure significantly. It will also teach you about how to apply these controls to the rest of your organization.
Making Sense of Cyber Security’s Alphabet Soup
Unless you work for the government, you would be hard-pressed to find an industry more in favor of acronyms than the world of security and compliance. Figure 1 shows just a subset of the acronyms associated with the cyber security issues and solutions.
Figure 1. The Alphabet Soup of Cyber Security.
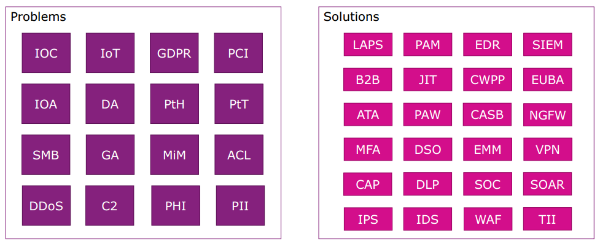
Source: Insight
Added to this growing alphabet soup of acronyms are a few other issues impacting an organization’s cyber security efforts:
- An increasing number of security point solutions now needing to be managed. It’s not uncommon to see upwards of 50+ point solutions at many medium to large organizations.
- A burgeoning mountain of log data from such solutions that often goes unchecked, until after the problem is found.
- A growing shortage of skilled IT security personnel to help manage the onslaught, and react appropriately to the increasing threat landscape.
- The on-going use of legacy security practices that continue to put organizations at increased risk through lack of innovation and adoption.
These factors make it difficult for an organization to control and protect against potential security threats—whether those exist on-premises or in one or more cloud environments.
The answer to many such challenges, however, may point to a future where security solutions, themselves, are increasingly cloud-based. To get ready for this future, organizations should begin looking now to learn more about dynamic, scalable cloud-based security solutions. No two are alike. Such solutions may ultimately offer one consolidated platform from which to manage user access and identity—regardless of the multiple cloud providers and cloud services being used by an organization.
It can be hard to make sense of this alphabet soup of acronyms and the sea of conflicting security priorities. Many organizations find it helpful to seek guidance from experts that help put such priorities into a working, high-level framework or architecture. In our experience, this helps to provide more context from which to view vendor offering and how they might fit into an organization.
