Home » access management
Articles Tagged with ''access management''
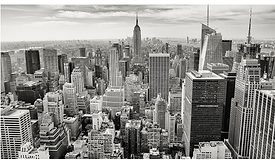
Five areas where centralized security systems are making urban centers safer
A centralized deployment reduces costs and is easier to use, giving public officials better tools for protecting their citizens.
May 25, 2021
Get our new eMagazine delivered to your inbox every month.
Stay in the know on the latest enterprise risk and security industry trends.
SUBSCRIBE TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing