Home » Publications » Security Magazine
Security Magazine

2014 May
Cover Story
Back to TopThe next national security crisis may be a lack of ability to mitigate or respond to such an attack because frankly, there’s no one available to mitigate the attack or respond to it.
Read More
Featured Articles
Back to TopFacilitating Better Healing with Visitor-Friendly Security
Being near family, surrounded by familiar and caring people, can help patients heal better and faster.
May 1, 2014
Managing Mass Communication in Tornado Alley
Tornado Alley is a colloquial term for the area of the United States where tornadoes are most frequent.
May 1, 2014
How to Protect an Ever-Expanding Perimeter
Four New York-area men were arrested after a BASE jumping stunt from atop One World Trade Center.
May 1, 2014
Adding Function, Lowering Cost with Video Management
It’s an ongoing and inevitable conundrum for security systems managers: not all end users are experts.
May 1, 2014
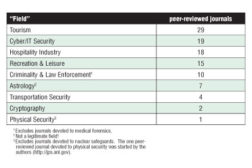
Does Enterprise Physical Security Count as a ‘Real’ Field?
We define physical security as measures taken to protect tangible physical assets from harm.
May 1, 2014
Secure the Enterprise with Effective Background Screening
Employment background screening helps employers identify qualified applicants and helps mitigate risk by improving workplace security and safety.
May 1, 2014
Columns
Back to TopManaging Security for Emergency Departments with High-Risk Patients
Hospital Emergency Departments are a truly unique environment.
May 1, 2014
Are Productivity Apps More Harm than Good?
According to the website “Tech Cocktail,” there are some “awesome apps” out there to make employees more productive at work.
May 1, 2014
Making Sense of LANs, MANs, WANs and More
Get to know Taylor Carr, Vice-President, Business Development & Integration for Securadyne Systems, and learn how Securadyne’s enterprise security executive customers are addressing cybersecurity in their enterprises.
May 1, 2014
Making Surveillance a Business Intelligence Necessity
There are two types of successful CSOs today: those that have cross-purposed their investment in video surveillance, and those that will.
May 1, 2014
Finding Sustainability's Purpose in Security
The most environmentally sustainable building in the world is the Change Initiative Building in Dubai, based on the LEED Commercial Interiors rating system.
May 1, 2014
Stopping Cybersecurity Breaches Means Rethinking Consequences
Would there be a greater return on investment if our information sharing focused less on enabling private sector victims to better duck and cover, and focused more on enabling the government to get the bad guys?
May 1, 2014
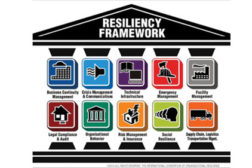
How to Add Resiliency to Your Risk Management Strategy
The latest buzzword these days is “Resiliency,” which for all intents and purposes is really nothing more than a new term for business continuity planning (BCP) in the private sector and continuity of operations planning (COP) in the public sector.
May 1, 2014
Get our new eMagazine delivered to your inbox every month.
Stay in the know on the latest enterprise risk and security industry trends.
SUBSCRIBE TODAY!Copyright ©2024. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing